Approximately 2.5 million people connect to the Tor network every day. Over 65,000 unique .onion addresses are active at any given time, and Tor Browser has been downloaded more than 200 million times. In 2026, the deep web and its more secretive subset, the dark web, look very different from the Silk Road era: the Tor Project is replacing its 23-year-old C codebase with a Rust rewrite, law enforcement arrested 270 vendors in a single operation, and major newsrooms still run onion mirrors for readers in censored countries.
Deep web, dark web, surface web: three layers you keep confusing
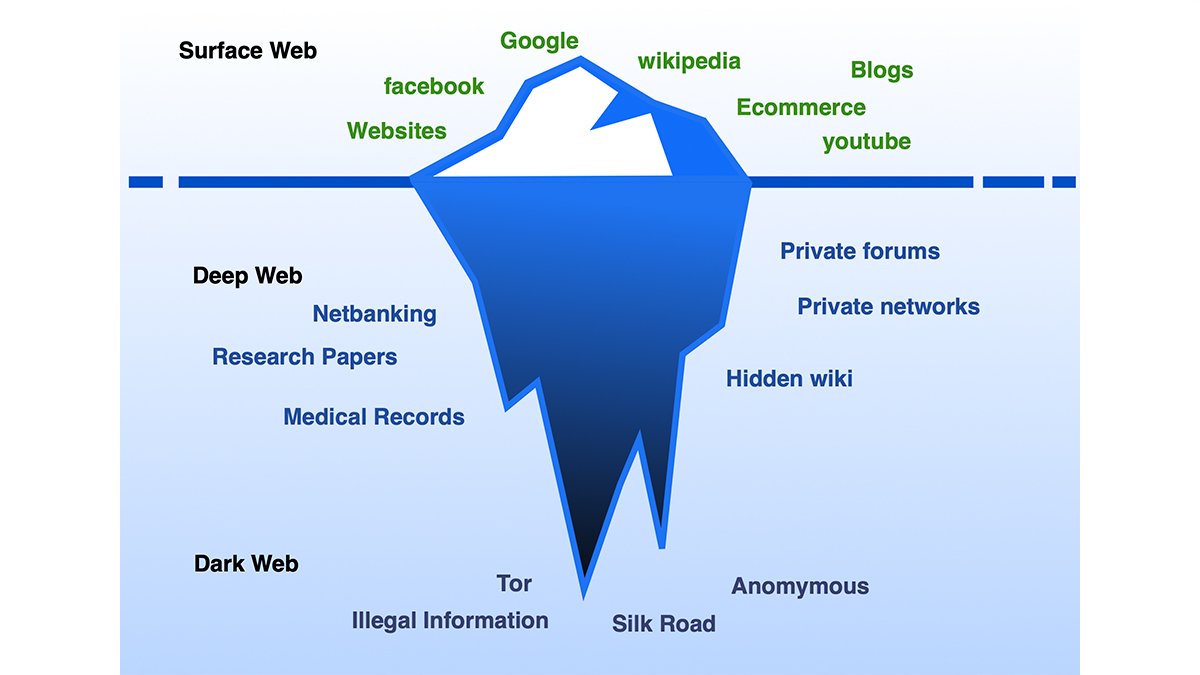
The surface web is everything indexed by Google and Bing. This article, Wikipedia, a company's public homepage — roughly 5–10% of all content online.
Everything search engines cannot reach is the deep web. Your Gmail inbox is deep web. So is your company's Jira board, your bank balance page, a hospital's patient database, a university's paywalled journals. By volume, the deep web dwarfs the surface. Nothing sinister about it — you use it every day without thinking.
A small, deliberately hidden slice of the deep web is the dark web. It requires special software to access and runs on overlay networks — Tor being the largest — where both the user and the server stay anonymous. Dark web sites use .onion addresses: long random strings that do not resolve in Chrome or Firefox. The .onion forum where someone is selling credentials stolen from those same Jira instances? That's the dark web. You cannot stumble onto it by accident.
| Parameter | Surface web | Deep web |
|---|---|---|
| Share of internet | 5–10% | ~90% (including dark web) |
| Indexed by Google | Yes | No |
| Requires special software | No | No (dark web subset: yes — Tor, I2P) |
| Examples | Wikipedia, news sites, public blogs | Email inboxes, bank dashboards, corporate wikis |
| Dark web examples | — | .onion sites: SecureDrop, NYT mirror, illicit markets |
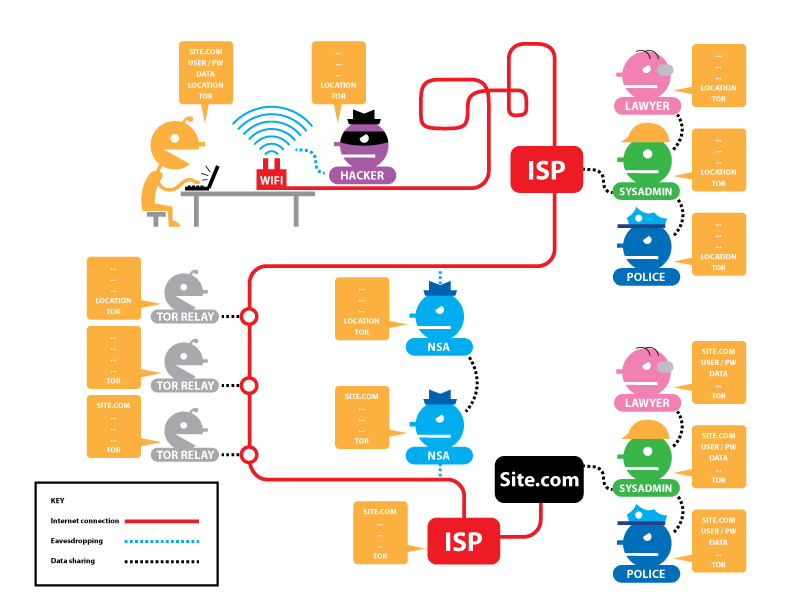
How Tor routes your traffic through three layers of encryption
Tor stands for "The Onion Router." The name describes its core mechanism: layered encryption. When you open a page through Tor Browser, your traffic passes through three relays — called the guard (entry) node, the middle node, and the exit node. Each relay peels off one layer of encryption, like layers of an onion.
The guard node knows your IP address but not your destination. The middle node knows neither. The exit node knows the destination but not your IP. No single relay in the chain can link the sender to the recipient. As of July 2025, the Tor network operated approximately 8,000 active relays worldwide.
For .onion sites, the traffic never leaves the Tor network at all. There is no exit node. Both the user and the server communicate through "rendezvous points" inside the network, which is why onion services can be hosted without revealing the server's physical location.
What Arti 2.0 means: Tor rewrites its engine from scratch in Rust
The Tor Project released Arti 2.0.0 on February 2, 2026. Arti is a complete rewrite of the original C-language Tor codebase — the same code that has powered the anonymity network since 2002 — in the Rust programming language. Arti 2.1.0 followed on March 3, 2026, adding further relay and RPC development.
Security drove the rewrite. The original C implementation accumulated two decades of technical debt: heap-based buffer overflows, use-after-free bugs, and memory corruption vulnerabilities documented in the CVE database. A 2023 penetration test found unmaintained C code from 2012 still running in one module. According to the Tor Project's own estimates, at least half of the security flaws found in C Tor become impossible in Rust, and many more become unlikely.
Arti cannot yet run as a relay — that feature is still under development. But it already functions as a SOCKS proxy for client connections, and the project is funded in part by a Zcash Community Grant that accelerated development from concept to production readiness in roughly two years. The old C implementation cannot be incrementally modernized because its modules are too tightly coupled; the Tor Project committed to a full rewrite rather than patching legacy code indefinitely.
Who actually uses Tor — and for what
Of the roughly 2.5 million daily Tor users, about 85% browse regular websites — they use Tor for privacy, not for hidden services. Only an estimated 6.7% connect to .onion addresses on any given day. One study of 400 .onion domains found approximately 45% hosted some form of illicit content. The other 55% included privacy tools, forums, mirrors of legitimate news organizations, and technical projects.
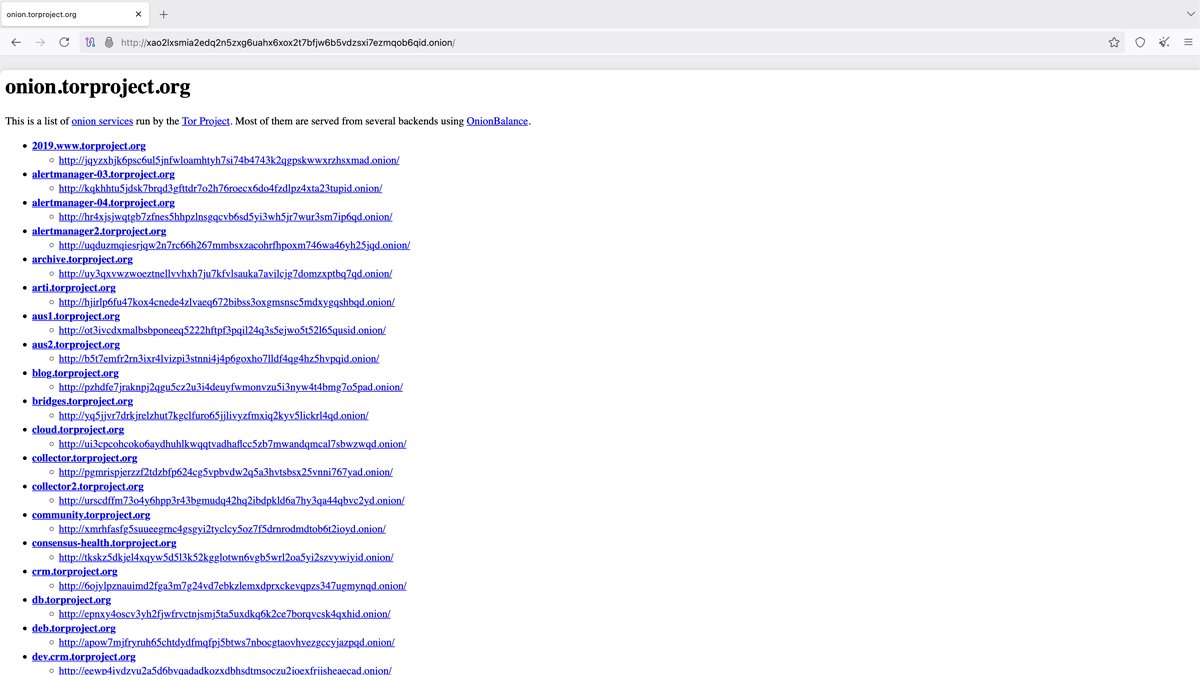
Several major organizations operate official .onion mirrors. The New York Times runs an onion site so readers in censored countries can access its reporting. The BBC launched its own Tor mirror. Facebook's onion address allows access in countries where the platform is blocked. ProPublica, the nonprofit investigative outlet, maintains a Tor presence. The CIA has its own .onion site for anonymous intelligence submissions. SecureDrop, the whistleblower platform designed by the late Aaron Swartz along with Kevin Poulsen and James Dolan, is used by dozens of newsrooms globally.
Proton Mail offers a verified onion service for encrypted email access over Tor. Riseup, a collective providing communication tools for activists, uses the dark web to keep its services available when governments block its clearnet addresses.
Dark web markets in 2026: smaller, more fractured, harder to reach
The era of giant one-stop dark web marketplaces is fading. Each successive takedown scattered vendors and buyers across smaller, more fragmented platforms.
| Marketplace | Active years | Scale | How it ended |
|---|---|---|---|
| Silk Road | 2011–2013 | 100,000+ users | FBI takedown (Oct 2013) |
| AlphaBay | 2014–2017 | 200,000 users, 250K listings | Operation Bayonet (Jul 2017) |
| Hydra | 2015–2022 | Largest by transaction volume | German/U.S. seizure (Apr 2022) |
| Archetyp | 2020–2025 | 600,000 users | Operation Deep Sentinel (Jun 2025) |
As of early 2026, the surviving ecosystem clusters around a handful of platforms: TorZon Market as a multi-purpose hub, STYX Market for financial fraud services, Brian's Club for stolen credit cards, Russian Market for breached credentials, and WeTheNorth for the Canadian market. None has achieved the scale of Hydra.
Criminal communities shifted sharply in 2025–2026 toward invite-only access, steep entrance fees, and premium membership tiers. After a wave of law enforcement seizures and Telegram's tightened moderation policies following its CEO's legal troubles in France in 2024, many groups retreated into gated forums like Exploit and RAMP, Russian-language platforms where entry requires referrals from established members or proof of technical capability. Data that used to be posted openly on BreachForums or Telegram channels now circulates behind paywalls.
Law enforcement operations: the 2025–2026 crackdown by the numbers
Operation RapTor, announced by the U.S. Department of Justice and Europol in June 2025, was the largest coordinated dark web operation to date. It resulted in 270 arrests across four continents, seizure of over $200 million in assets, and record quantities of fentanyl, opioids, firearms, and counterfeit currency. The operation built on intelligence from prior takedowns of Nemesis, Tor2Door, Bohemia, and Kingdom markets.
This historic international seizure of firearms, deadly drugs, and illegal funds will save lives. Criminals cannot hide behind computer screens or seek refuge on the dark web.
— Attorney General Pam Bondi, U.S. Department of Justice
Operation Checkmate, confirmed by the DoJ on July 24, 2025, seized the infrastructure of the BlackSuit ransomware group: domains, servers, and $1.09 million in laundered cryptocurrency. Chief Guy Ficco of IRS Criminal Investigation called RapTor "the largest and most impactful takedown to date," noting over $200 million in seized assets. Operation Deep Sentinel took down Archetyp Market in June 2025, leading to the arrest of its alleged German administrator in Barcelona and freezing approximately €7.8 million in assets.
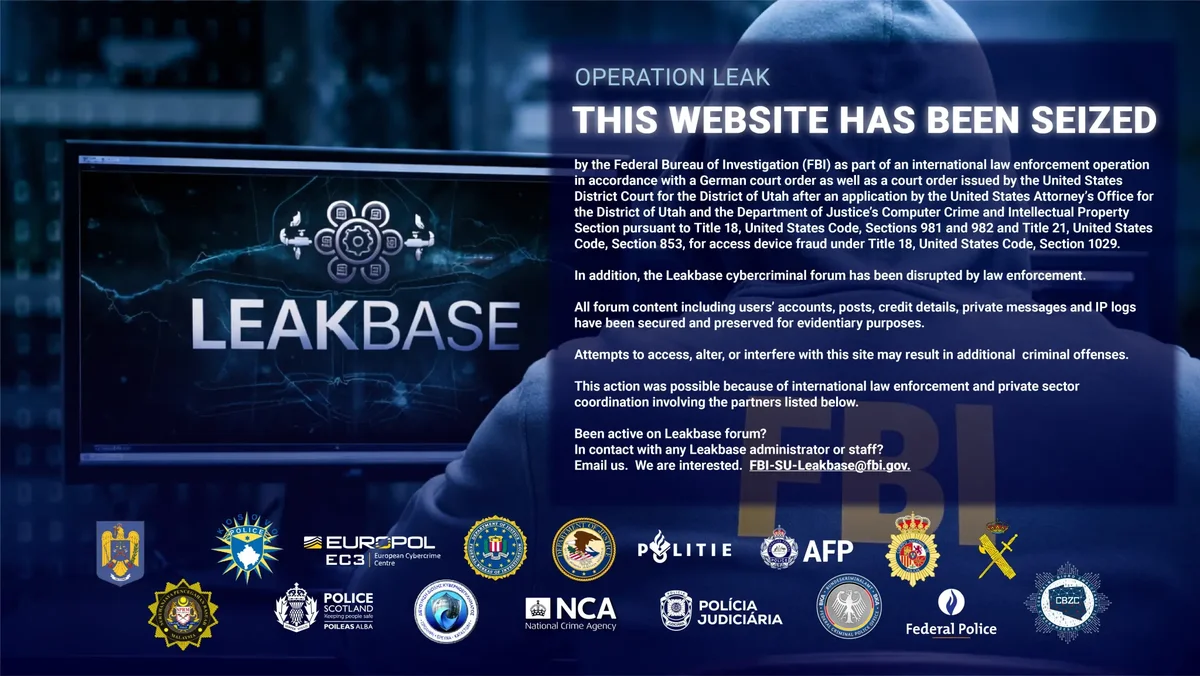
On March 3–4, 2026, Europol coordinated the most recent operation: the takedown of LeakBase, a cybercrime forum with 142,000 registered users, 32,000 posts, and over 215,000 private messages. Authorities in 14 countries participated. A two-phase approach, first arresting 37 of the most active users, then seizing the platform's infrastructure, reflects a shift in tactics: targeting users, not just servers.
What began as a shadowy forum for stolen data has now been dismantled, and those who believed they could hide behind anonymity are being identified and held accountable.
— Edvardas Šileris, Head of Europol's European Cybercrime Centre, on the LeakBase operation
The U.S. Congress introduced the Dark Web Interdiction Act of 2025 (H.R.6104 / S.1975) to create a dedicated FBI task force for dark web investigations, codifying the kind of interagency coordination that operations like RapTor relied on ad hoc.
Iran, censorship, and the other side of Tor
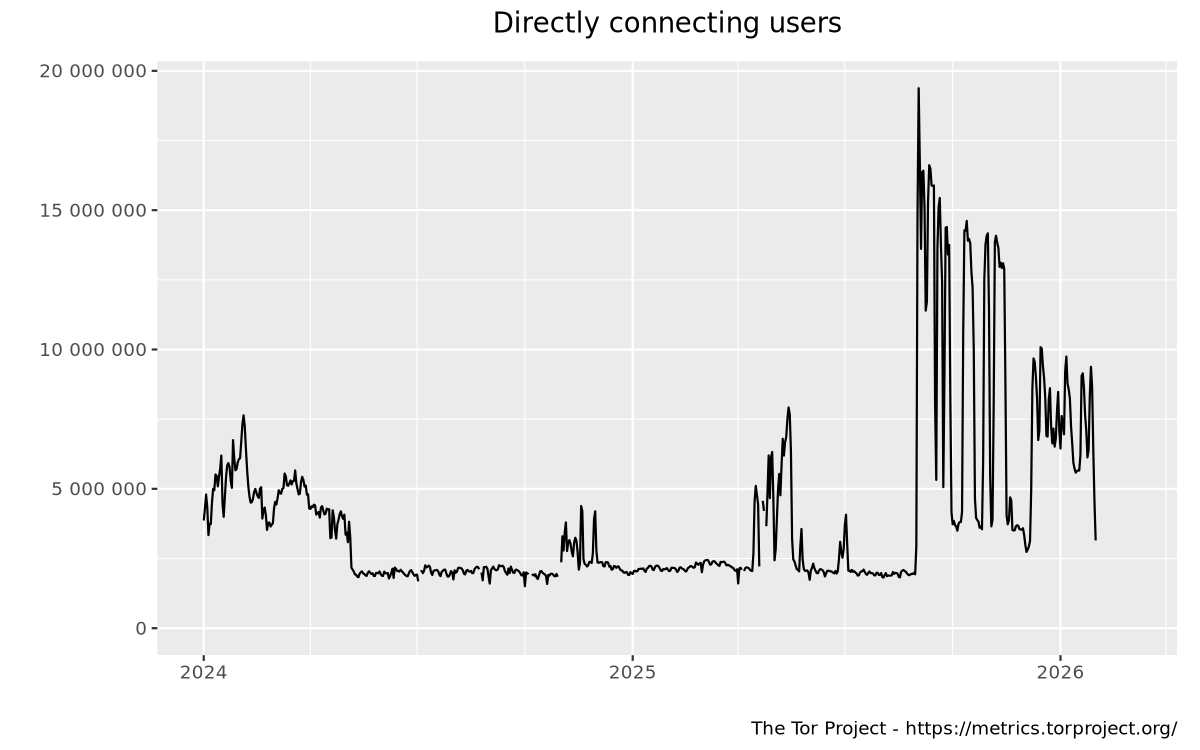
Tor usage spikes when governments tighten internet controls. Iran imposed a 2.5-week internet shutdown in January 2026 during nationwide protests. Snowflake bridge usage — one of Tor's primary censorship circumvention tools — tripled between January 21 and January 27, according to the Tor Project's Snowflake operations report. By February 2026, traffic gradually returned to former levels.
| Country | Avg. daily Tor users | Share of global Tor traffic |
|---|---|---|
| Russia | ~12,194 | ~23.7% |
| United States | ~10,792 | ~20.96% |
| Iran | ~3,778 | ~7.34% |
| Germany | Top 10 | Combined U.S. + Germany: ~68% |
Source: 99firms analysis of Tor Metrics data; SQ Magazine, 2025.
Bridges, non-public relays that help users reach Tor when direct access is blocked, remain essential. Pluggable transports disguise Tor traffic to evade deep packet inspection. In censored countries, bridge adoption can spike by factors of 50–70x during crackdowns, according to SQ Magazine's analysis. The Tor Project quietly launched a beta Android VPN app to route app-level traffic through the network, extending protection beyond the browser.
Tails 7.5, released February 26, 2026, is the latest version of the amnesic operating system designed to run entirely from a USB drive and route all traffic through Tor. Earlier releases in January and February 2026 were emergency patches for critical vulnerabilities in the Linux kernel and OpenSSL.
How to check if your data is already on the dark web
The dark web may already have your data. Credential leaks, breached databases, and infostealer logs circulate on dark web forums and marketplaces daily. The 2025 Flare report analyzed 18.7 million infostealer logs and found that 2.05 million contained enterprise identity provider credentials.
Practical steps: use a reputable breach-monitoring service (Have I Been Pwned is free and well-maintained). Enable multi-factor authentication — preferably hardware-key or app-based, not SMS. Use unique passwords for every service. If you receive a breach notification, change the password immediately and check whether the same credential was reused elsewhere. Google discontinued its dark web report feature in 2026, shifting the responsibility to individual monitoring.
Do not attempt to access dark web marketplaces, forums selling stolen data, or any illegal services. Browsing the dark web carries real risks: scams, malware, phishing pages designed to steal credentials, and potential legal consequences depending on your jurisdiction. Tor Browser does not validate the legitimacy of the sites you visit.
What Tor Browser looks like in practice (and what it cannot do)
Tor Browser is built on Mozilla's Firefox Extended Support Release (ESR). The latest stable version is 15.0.7, released February 24, 2026, with alpha version 16.0a3 in testing. It adds first-party isolation, uniform settings that resist fingerprinting, and automatic clearing of cookies and history on exit. The default search engine is DuckDuckGo. It runs on Windows, macOS, Linux, and Android. On iOS, WebKit restrictions force a different codebase with different tradeoffs.
Tor Browser does not make you invincible. Your ISP can see you are using Tor. Logging into a service with your real name links your identity to that session. Opening downloaded files outside the browser may bypass Tor entirely. Enabling plugins or scripts expands your attack surface. Tor protects the network path — not your behavior.
Speed remains a constraint. Traffic takes multiple hops through bandwidth-limited relays. Text-heavy sites load fine. Video streaming, large downloads, and real-time communication are slow or unreliable. Many content delivery networks treat Tor exit nodes as high-risk, so CAPTCHAs and outright blocks are common on mainstream websites.
Tor is legal almost everywhere — with exceptions
Downloading and using Tor Browser is legal in the vast majority of countries. A handful of states — including China, Russia, Iran, and Turkmenistan — restrict or block access, though enforcement varies. Using Tor does not make illegal activity legal, just as using a car does not legalize bank robbery. The technology is neutral; the applications determine legality.
Tor was originally developed by the U.S. Naval Research Laboratory in the mid-1990s. Mathematician Paul Syverson and computer scientists Michael Reed and David Goldschlag created the onion routing concept to protect American intelligence communications. The alpha version launched on September 20, 2002, built by Syverson, Roger Dingledine, and Nick Mathewson. In 2004, the Naval Research Laboratory released the code under a free license, and the Electronic Frontier Foundation began funding continued development.
Arti relay support is still in progress — once complete, it will allow the entire Tor network to run on Rust, eliminating the C codebase entirely. The latest stable Tor Browser release is version 15.0.7, published February 24, 2026, with alpha 16.0a3 already in testing. The network that started as a U.S. Navy project in 2002 now runs on 8,000 volunteer relays across dozens of countries, serving 2.5 million daily users — government-built, community-maintained, and under more pressure than at any point in its 24-year history.
- Оглавление генерируется автоматически при просмотре






