
The US Department of Justice disrupted command-and-control infrastructure behind four IoT botnets on March 19, 2026. The Aisuru, KimWolf, JackSkid, and Mossad botnets had compromised 3+ million devices worldwide and launched more than 316,000 DDoS attack commands. Cloudflare linked the combined network to a record 31.4 Tbps attack lasting 35 seconds in November 2025.
German police identified two suspected administrators. One is a 22-year-old in Canada, the other a 15-year-old in Germany, according to KrebsOnSecurity. Officers searched their residences and seized data storage devices and cryptocurrency.
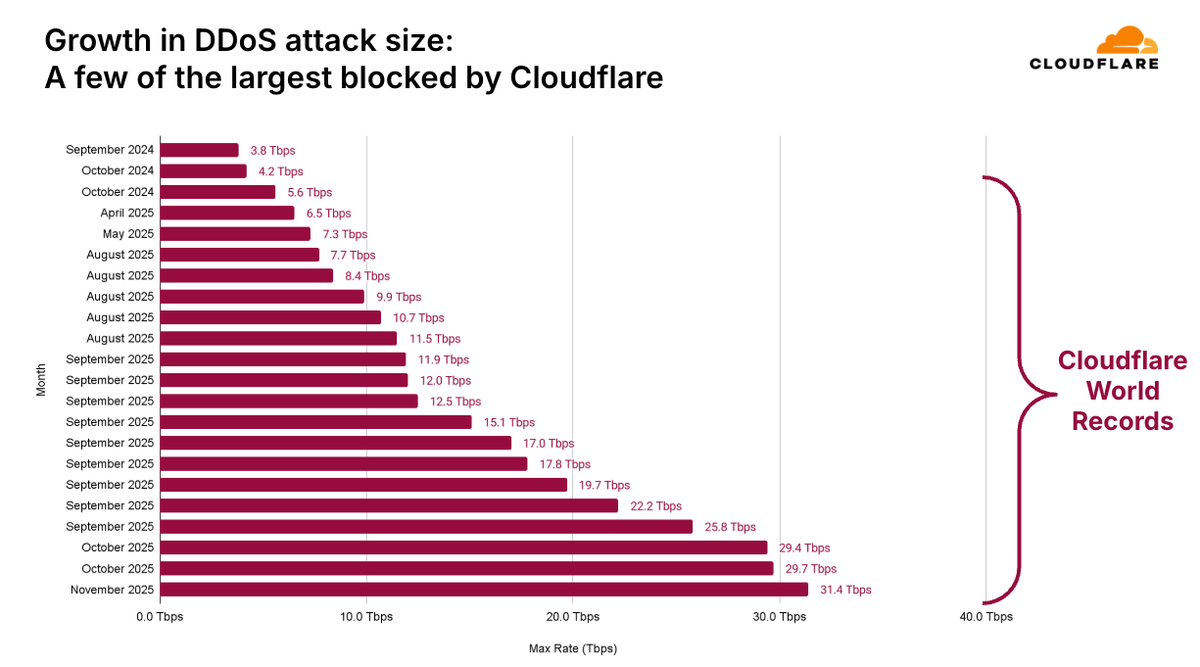
Aisuru emerged in late 2024 and became the dominant DDoS botnet by mid-2025. It issued 200,000+ attack commands. In May 2025, Aisuru hit KrebsOnSecurity with a flood exceeding 6.3 Tbps. Microsoft blocked a separate 15.72 Tbps attack from 500,000 IP addresses on Azure five months later.
Broadband providers reported 1.5 Tbps floods from infected customer devices. Bursts above 4 Bpps (billion packets per second) caused router line card failures.
Built on the leaked Mirai source code, this TurboMirai variant supports more than DDoS. Credential stuffing, AI-driven web scraping, spamming, and phishing are all in the toolkit. Floods use UDP, TCP, and GRE with randomized ports and flags.
The problem is, there are just so many devices out there that are vulnerable that two things happened — first, Kimwolf proved to be incredibly resilient.
— Ryan English, security researcher, Lumen Black Lotus Labs
KimWolf is Aisuru's Android-focused successor, spawned in October 2025. XLab researchers tracked 1.8+ million infected devices and 1.7 billion DDoS commands. The botnet targets Android TV boxes. It encrypts data with Stack XOR, hides C2 traffic behind DNS-over-TLS, and authenticates commands with elliptic curve digital signatures. Recent versions use EtherHiding (blockchain domains) to resist takedowns.
Researchers who seized one C2 domain observed 2.7 million IP addresses connecting across three days.
Operators rented KimWolf-infected devices as a residential proxy network. Third parties paid to route traffic through compromised TVs and routers without the owners' knowledge.
Both KimWolf and JackSkid infected devices behind firewalls. Synthient publicly disclosed the propagation vulnerability on January 2, 2026. JackSkid averaged 150,000+ daily victims in early March 2026, peaking at 250,000 on March 8, according to Lumen Black Lotus Labs. Mossad averaged 100,000+ daily victims in the same period.
Lumen null-routed nearly 1,000 C2 servers used by Aisuru and KimWolf.
DCIS (Defense Criminal Investigative Service) executed seizure warrants targeting US-registered domains, virtual servers, and other infrastructure. Victims included the Department of Defense Information Network (DoDIN), telecoms, and enterprises worldwide. In some cases, operators demanded extortion payments.
Today's disruption of four powerful botnets highlights our commitment to eliminate emerging cyber threats to the Department of Defense and its warfighters.
— Kenneth DeChellis, Special Agent in Charge, DCIS Cyber Field Office
Nearly two dozen partners assisted. Akamai, AWS, Cloudflare, Google, Lumen, Nokia, PayPal, Sony Interactive Entertainment, QiAnXin XLab, and Europol's PowerOff team were among those credited by the DOJ.
Total DDoS attacks doubled in 2025 to 47.1 million globally. Network-layer attacks tripled year-over-year. Most lasted under 10 minutes, too fast for human-led mitigation.
Europol's PowerOff has targeted DDoS-for-hire storefronts since 2017. In December 2024, the DOJ seized 27 booter domains, but this operation went further and hit the botnets themselves.
C2 infrastructure is down, but the devices remain infected. Millions of DVRs, cameras, and routers with default credentials and no update path are still online and available for the next botnet. Nokia Deepfield detected a new Mirai variant targeting Android TV boxes via ADB on March 18, one day before the takedown announcement.
Update firmware on DVRs, cameras, and routers. Change default passwords. Disable remote management interfaces not in active use. Cloudflare offered a sense of scale. The combined attack capacity equaled "the combined populations of the UK, Germany, and Spain all simultaneously hitting 'enter'."
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







