BreachForums has fractured. Six months after the FBI seized the cybercrime forum, rival reboots run by competing operators all claim to be the legitimate successor. ShinyHunters publicly disavowed two of the most visible claimants on March 26, calling the aliases "N/A" and "Indra" false personas attached to lookalike forums. The disavowal landed in the middle of a wave of doxxing threats, conflicting manifestos, and disinformation warnings from threat intelligence firms.
Pattern beats any single claim here. Every recent attribution against an alleged BreachForums operator has come from an anonymous source. Each one contradicted another anonymous source. All of them arrived during an active feud between people who used to share infrastructure.
How the forum fractured
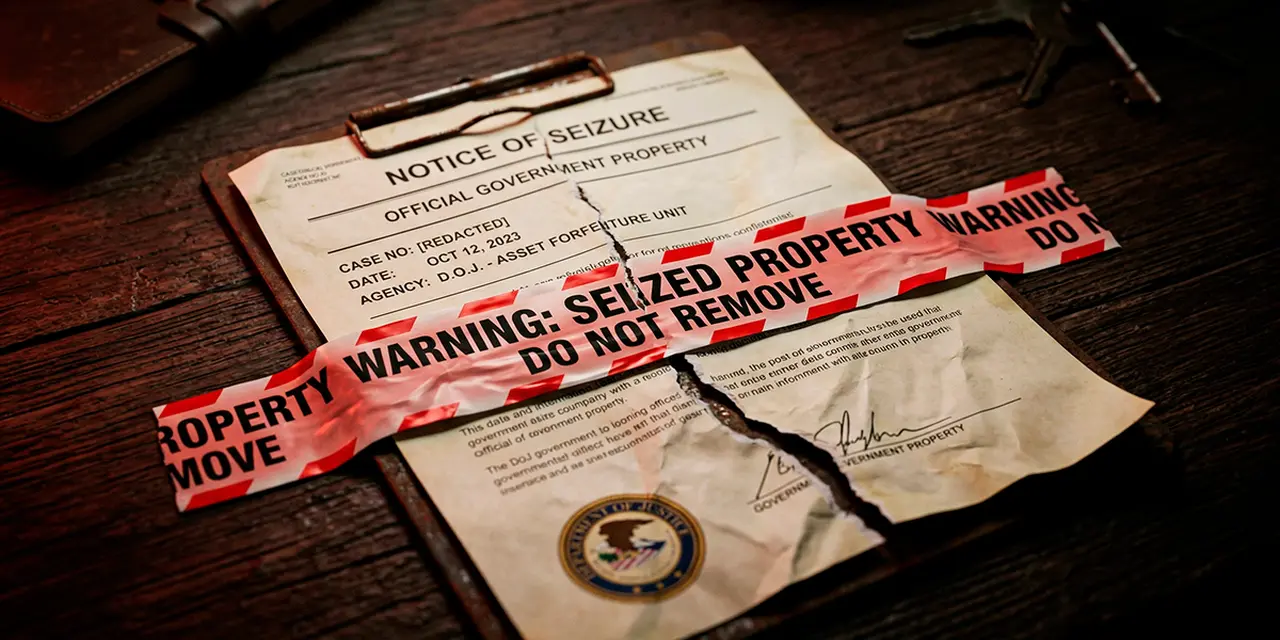
The original BreachForums fell on October 10, 2025, when the FBI seized the domain. ShinyHunters has since stated this was the moment they stopped operating the forum. Every site carrying the BreachForums name since then has been a reboot under a new operator. Most use a recycled database from before the seizure.
A first reboot surfaced in December 2025 under an alias called "Indra." A second wave landed in mid-March 2026. An operator using the alias "N/A" took over what community members later characterised as an exit scam. According to BreachAware research, allegations surfaced that N/A had pocketed roughly $4,000 by selling forum infrastructure to an associate linked to a threat actor. That sale allegedly included the database itself. Moderators publicly threatened N/A in a now-removed post. The operator was given five days to make contact before being doxxed in front of "hundreds of thousands of people."
BreachForums then disappeared on March 15. It reappeared on March 25 under a new domain and a new alias, "Caine," using an earlier backup. The moderation team resigned two days later after concluding Caine was the same person as N/A.
A separate operator launched another version on a .ai domain in late March. They used the alias "X" — not the social media platform — and claimed to have rebuilt the forum independently.
ShinyHunters disowns the lot
On March 26, 2026, ShinyHunters published a statement disavowing the entire post-seizure ecosystem. The group stated that "false personas going by 'N/A' and 'Indra' were successfully able to restore a similar-looking 'legitimate' forum." None of the current BreachForums instances are authentic, the group said. ShinyHunters threatened to leak full forum backups if the lookalike sites continued operating.
The implication matters for attribution. If ShinyHunters' position is accepted, "N/A" is not the administrator of historical BreachForums at all. N/A is an opportunistic operator who restored a clone after the legitimate forum was seized. Whether anyone has correctly identified the human behind that alias becomes a secondary question. The first question is whether the alias administers anything that should be called BreachForums in the first place.
ShinyHunters reiterated the denial in early April after a third self-proclaimed operator surfaced. Information Security Media Group reported on April 3 that researchers had found inconsistencies in the parallel claims. The post was updated on April 5 to include the ShinyHunters denial in full.
The January database and a disinformation warning
Most current attribution work for BreachForums traces back to a single dataset. On January 9, 2026, a self-described former ShinyHunters member published the BreachForums user database alongside a 23-page manifesto naming alleged forum operators. The database contained records for 323,986 users.
The manifesto named one person as the human behind the aliases N/A and Indra. It also assigned other real-world names to other forum aliases. None of those names have been independently confirmed by law enforcement or by any mainstream cybersecurity outlet.
Threat intelligence firm Resecurity analysed the leaked database and reached a different conclusion. Resecurity warned that the dataset should not be interpreted as authentic. The firm assessed it as likely "a method to plant disinformation by actors in order to mislead investigations." Some IP addresses in the leaked records were loopback addresses such as 127.0.0.9. Resecurity interpreted those as a deliberate operational security measure by the people administering the forum.
Any chain of attribution that begins from records inside a database flagged as disinformation inherits that uncertainty. This is the dataset on which most of the public N/A attribution work has been built.
Conflicting names for the same alias
Two separate sources have now named two different people as the human behind the alias N/A. The January manifesto named one person. An anonymous social media account named a completely different person on April 6.
Neither source has published technical evidence. No IP logs, no PGP signature analysis, no server artefacts, no chat exports have been released alongside either claim. ShinyHunters are the people in the best historical position to confirm or deny these attributions. They have publicly stated that the alias in question belongs to a false persona rather than a legitimate operator.
Two unconfirmed names for the same alias is not corroboration. It is a contradiction that makes both attributions less credible.
In the BreachForums orbit, doxes are routinely deployed as instruments of internal feud and retaliation, not as journalism. The moderation team threatened a public dox of N/A two weeks before the latest attribution surfaced. Treating these claims as confirmed identifications without independent verification is how publications get used by one side of an ongoing war.
Doxxing as a feud weapon, not investigation
This pattern is normal for the corner of cybercrime underground around BreachForums. BreachAware documented a parallel feud in late March. Moderators of one BreachForums spin-off accused the admin of another, "Hasan," of hijacking the BreachForums identity. According to BreachAware, the moderators allegedly published Hasan's driver's licence photo, photos of his home, and personal details about family members.
That earlier dox illustrates the dynamic. In this ecosystem, accusations of identity are weaponised as part of business disputes. They are not produced by independent investigation. Any single-source attribution against any named individual in this space has to be approached with that pattern in mind.
The chronology of the recent N/A attribution campaign fits the pattern exactly. ShinyHunters disavowed N/A on March 26. Moderators publicly threatened N/A with a full dox days before that. The latest anonymous attribution surfaced eleven days after the disavowal and roughly two weeks after the dox threat. None of this looks like independent investigative reporting that happened to land in the middle of an unrelated drama. It looks like the next move in the drama itself.
What law enforcement actually confirmed
Every confirmed identification of a BreachForums operator has come from law enforcement action. Not from anonymous social media posts.
The first BreachForums was founded in March 2022 by Conor Brian Fitzpatrick. He was 19 at the time and used the alias "pompompurin." Fitzpatrick was arrested in March 2023 in Peekskill, New York. He later pleaded guilty to charges including possession of child pornography and was sentenced to time served and supervised release. Subsequent operators identified through arrests or court filings include "Baphomet," reportedly arrested in May 2024, and "IntelBroker," arrested in February 2025. In June 2025, French police arrested four more administrators using the aliases Hollow, Noct, Depressed, and a person operating under the ShinyHunters alias.
None of the post-October 2025 reboot operators have been identified by name in any court filing or law enforcement statement. Every name circulating in the public conversation comes from one of three places. An anonymous source. A leaked database flagged as potential disinformation. A manifesto written by a self-described former insider.
What this means for readers
Treating cybercrime forum doxes as journalism is how publications become participants in feuds rather than observers of them. The conditions in this case are clear. An anonymous account publishes a claim about a real person. No technical evidence is released. The people best positioned to confirm or deny the claim have explicitly disavowed the alias under discussion. The claim arrives during an active doxxing war between competing operators. Under those conditions, the responsible move is to cover the dispute, not amplify the attribution.
The actual story is the dispute. After six months of reboots, splinter forums, and competing claims, no one publicly knows who runs BreachForums today. The people who used to run it say nobody legitimate does. The dataset most attribution work depends on has been flagged as likely disinformation. Two anonymous sources have named two different people as the same alias. None of this is settled. None of it should be reported as if it were.
For defenders and threat intelligence teams tracking the BreachForums namespace, the practical takeaway is direct. Current claims of administrator identity are unreliable and operationally dangerous to act on. For everyone else, the takeaway is simpler. The attribution machinery around BreachForums is adversarial and unverified. Anyone repeating single-source dox claims is participating in the machinery rather than reporting on it.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







