The full source code of Anthropic's Claude Code CLI tool was publicly accessible on the npm registry. Security researcher Chaofan Shou discovered the exposure on March 31, 2026. The npm package @anthropic-ai/claude-code shipped a 57 MB source map file containing the entire original codebase.
Gabriel Anhaia's analysis on DEV.to counted approximately 1,900 files and over 512,000 lines of TypeScript. Source map files are standard build artefacts that map minified code back to original source. They contain a sourcesContent array with raw, unminified source code embedded as strings inside a JSON structure.
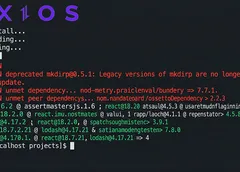
Claude Code uses Bun's bundler, which generates source maps by default. The .map file was not excluded via .npmignore or bundler configuration.
Anyone who ran npm pack @anthropic-ai/claude-code could access the full original source.
System prompts and security boundaries were exposed. The codebase includes the tool permission model, protected file lists, path traversal prevention, and the prompt engineering behind Claude Code's permission explainer. "Tengu" appears hundreds of times as a prefix for feature flags and analytics events, likely Claude Code's internal project codename. Another codename, "Capybara," is also referenced.
Kuberwastaken found constants/betas.ts, a file listing every beta feature Claude Code negotiates with the API. Identifiers include interleaved thinking, 1M token context window, structured outputs, web search, and advanced tool use. A "fast mode" and effort level control are also present.
Source map leaks are not novel in the npm ecosystem. The cause is almost always a build pipeline that generates.mapfiles by default and a publish step that fails to exclude them. Adding*.mapto.npmignoreprevents the exposure. The fact that this was missed suggests the publish pipeline did not include a pre-publish audit checking for unintended file inclusion.
Four unreleased systems are visible in the codebase. Kuberwastaken's analysis identified KAIROS, an "always-on" persistent assistant mode gated behind compile-time feature flags. KAIROS maintains daily log files, receives periodic prompts to decide whether to act, and has exclusive tools including push notifications and pull request monitoring. It operates under a 15-second blocking budget to avoid disrupting user workflow.
ULTRAPLAN offloads complex planning to a remote cloud container. It runs Opus 4.6 with up to 30 minutes of compute time. A browser-based UI lets the user watch the plan develop and approve or reject it.
Buddy is a Tamagotchi-style companion pet system with 18 species across five rarity tiers. Shiny variants have a 1% chance, and a Shiny Legendary rolls at 0.01%. Species names are obfuscated via String.fromCharCode() arrays. The code references April 1 through 7, 2026, as a teaser window, with full launch gated for May 2026.
Dream runs as a background memory consolidation engine. It triggers after 24 hours and five sessions since the last run. The subagent reads memory files, consolidates new information, converts relative dates to absolute, and prunes MEMORY.md to under 200 lines. It has read-only bash access.
A multi-agent coordinator is also in the code. Activated via environment variable, it transforms Claude Code from a single agent into an orchestrator spawning parallel workers.
The most discussed finding is "Undercover Mode" in utils/undercover.ts. When active, it injects instructions into the system prompt. The AI is prohibited from including internal codenames, unreleased version numbers, Slack channels, or the phrase "Claude Code" in commit messages and PR descriptions. The instruction explicitly states "Do not blow your cover," according to the leaked source.
Undercover Mode activates automatically unless the repository remote matches an internal allowlist, with no force-off option. The subsystem confirms Anthropic employees use Claude Code to contribute to external open-source repositories. The code was dead-code-eliminated from external builds, but source maps bypass dead code elimination because they contain the pre-elimination source.
The exposed codebase gives adversaries a complete map of Claude Code's security architecture, including the permission model, tool boundaries, protected file lists, and the logic governing what actions require user approval. Access to source code accelerates discovery of exploitable weaknesses. Whether anyone acts on this depends on the attack surface Claude Code presents, but the information is now permanently public.
The Axios npm supply chain attack happened on the same day. The two incidents are unrelated in mechanism. One is a packaging error, the other an account takeover. Both expose the same structural reality about npm packages often containing more than developers expect.
Anthropic has not issued a public statement on the exposure as of publication.
Development teams should check their own npm packages for .map files. Run npm pack --dry-run and inspect the file list before every publish. If source maps are present, original source code is public.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.