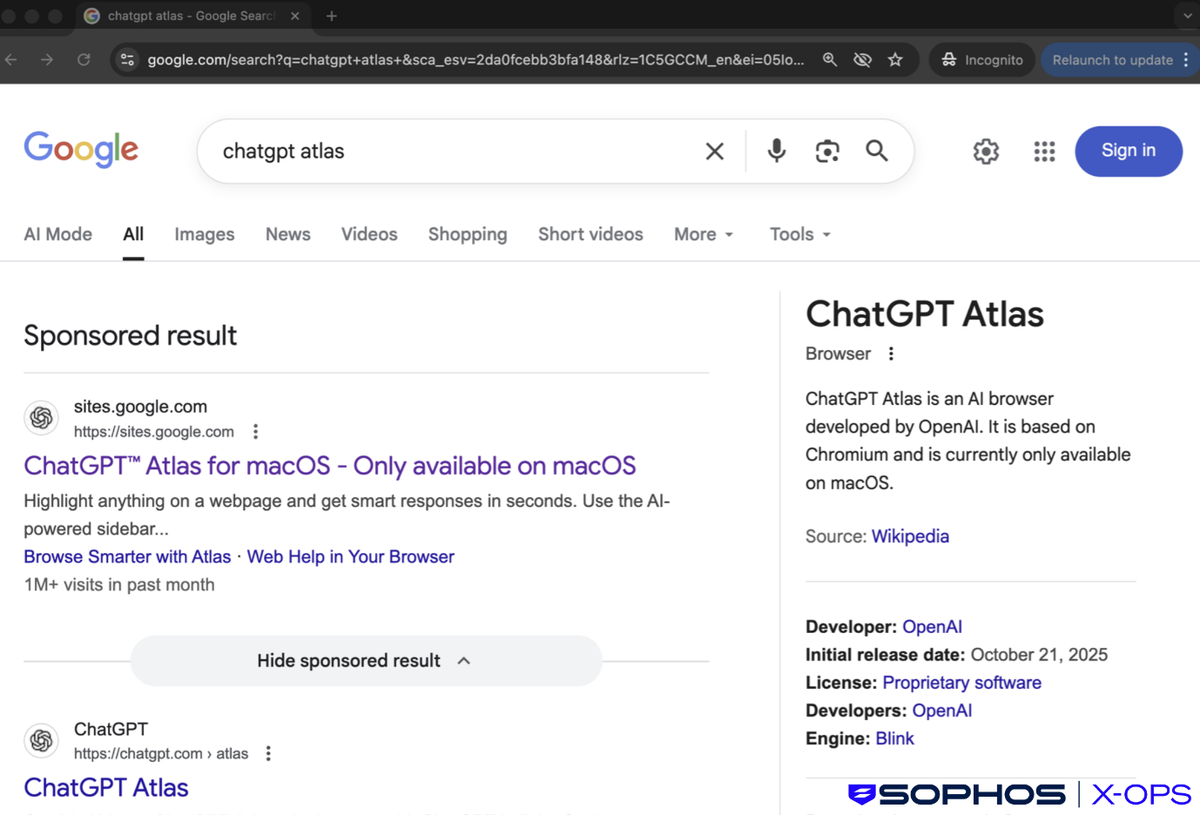
Three ClickFix social engineering operations distributed the MacSync infostealer to macOS between November 2025 and February 2026. Sophos X-Ops tracked the campaigns, which promoted bogus AI software through Google sponsored search results. Sophos telemetry recorded over 50,000 clicks on malicious domains within days of each deployment.
Pillar Security counted 20+ separate ClickFix operations hitting AI and developer products in February and March 2026. Seven of those 20 focused exclusively on macOS.
ClickFix requires no software exploit. The attacker builds a reason for the person to open Terminal and paste an obfuscated string. The November 2025 round advertised "OpenAI Atlas browser" through Google Ads. Clicks led to a Google Sites decoy with instructions to run a Terminal input. That input fetched a Bash script, requested the system password, and ran MacSync as a MachO binary.
The December 2025 round weaponized shared ChatGPT conversations. Attackers authored "Mac system cleanup" guides and shared them via unique chatgpt.com URLs. They promoted those links through Google Ads for cleanup-related queries. People who followed the guide reached GitHub-themed landing destinations where they pasted a second malicious string. Guardio Labs head Nati Tal confirmed the chain.
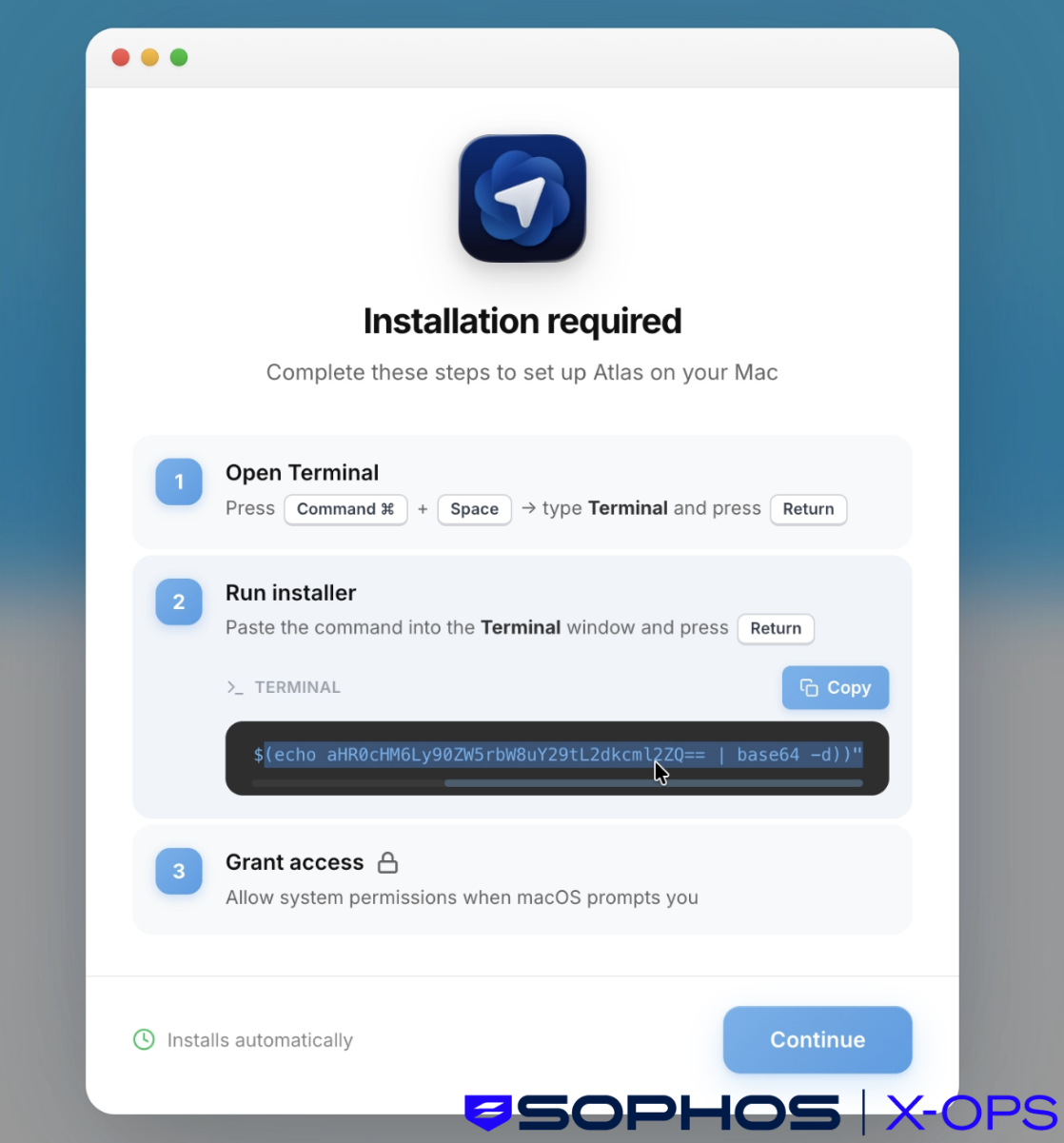
Unlike traditional exploit-based attacks, this method relies entirely on user interaction – usually in the form of copying and executing commands – making it particularly effective against users who may not appreciate the implications of running unknown and obfuscated terminal commands.
— Sophos X-Ops researchers Jagadeesh Chandraiah, Tonmoy Jitu, Dmitry Samosseiko, and Matt Wixey
The February 2026 round deployed a new MacSync variant hitting Belgium, India, and the Americas. Shell-based loaders authenticate to C2 infrastructure using API keys. Dynamic AppleScript payloads run entirely in memory, leaving no disk artifacts. The malware harvests credentials, keychain databases, and cryptocurrency wallet seed phrases, including injecting code into Ledger Live to capture master keys.
Stolen files are compressed and exfiltrated in segmented uploads. The loader relaunches as a background daemon for persistence.
While traditional ClickFix attacks need to manufacture a reason for the user to run a command: a fake CAPTCHA, a fabricated error message, a bogus system prompt — InstallFix doesn't need any of that. The pretext is simply the user wanting to install legit software.
— Push Security
Push Security coined "InstallFix" for a parallel variant that skips pretexts entirely. Attackers host counterfeit download destinations for products like Claude Code on Cloudflare Pages, Squarespace, and Tencent EdgeOne. On macOS, the shell input drops Atomic Stealer. On Windows, PowerShell fetches a Chrome extension within a malicious HTA file that launches the Alien infostealer in memory via an obfuscated .NET loader.
AI/vibe coding tool users skew heavily toward macOS, and macOS users tend to have higher-value credentials (SSH keys, cloud tokens, cryptocurrency wallets). The ClickFix/InstallFix technique is uniquely effective against developers because
— Eilon Cohen, researcher, Pillar Securitycurl | shis a legitimate installation pattern. Homebrew, Rust, nvm, and many other developer tools use this exact pattern. The malicious commands hide in plain sight.
ClickFix has already reached the enterprise perimeter. In December 2025, Sophos documented the first known ClickFix-to-ransomware chain. A person visited a compromised website, followed CAPTCHA prompts, and loaded NetSupport Manager RAT. StealC V2 followed. One month later, stolen credentials opened the network via a Fortinet VPN, leading to Qilin ransomware deployment.
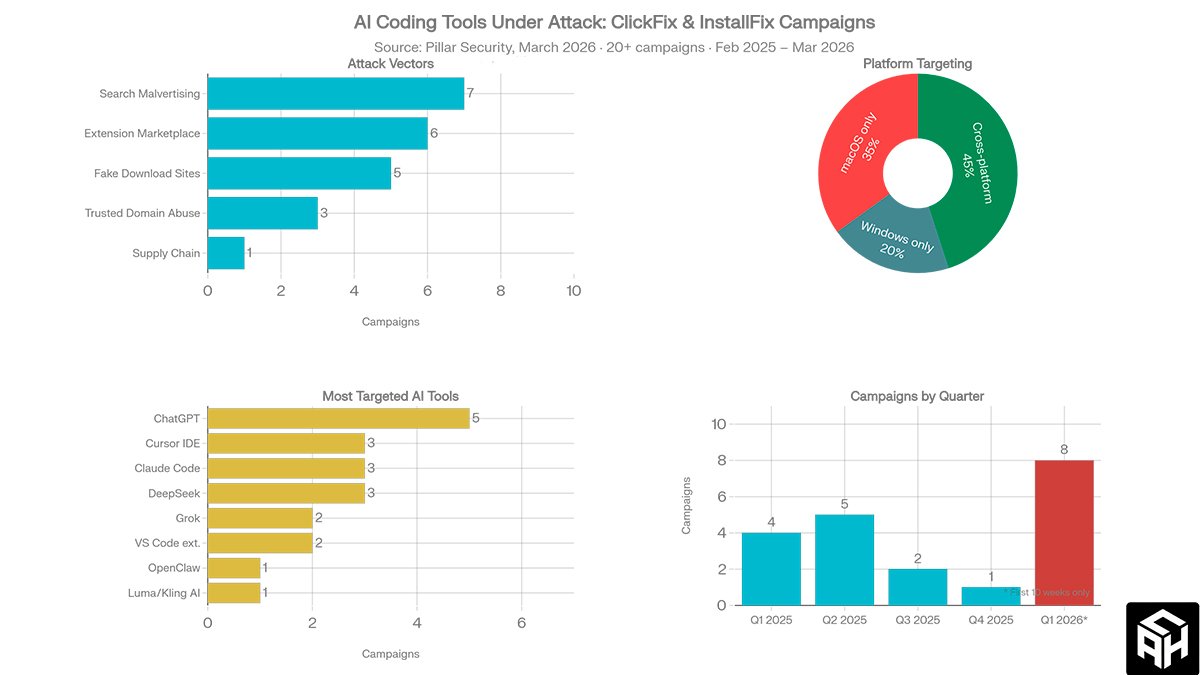
Rapid7 found 250+ infected WordPress domains across 12 countries distributing ClickFix lures that impersonate Cloudflare verification prompts. On Windows, the end goal includes StealC, Vidar, Impure Stealer, and VodkaStealer.
Sophos explicitly warned that phishing-resistant authentication (FIDO2) does not defend against ClickFix. The method operates at the endpoint. The person voluntarily runs software on their own machine.
Jamf Threat Labs documented a further MacSync evolution. A code-signed, notarized Swift application shipped as a DMG (zk-call-messenger-installer) bypasses macOS Gatekeeper entirely and requires no Terminal interaction. Microsoft Defender Experts confirmed active exploitation of MacSync alongside DigitStealer and Atomic Stealer in a February 2026 advisory.
The
— Artem Safonov, Threat Analyst at AnonHavencurl | shpattern is the most dangerous blind spot in developer security today. Homebrew, Rust, and nvm trained an entire generation of developers to paste Terminal strings from the web without reading them. ClickFix and InstallFix exploit that muscle memory. No patch fixes it.
Any instruction to paste a Terminal string from a search-ad website should be treated as hostile. Organizations should monitor for suspicious osascript and curl activity from user sessions. Check Ledger Live and other crypto wallet apps for unauthorized tampering. WordPress administrators should scan for injected JavaScript in templates. Sophos detection signatures OSX/InfoStl-FQ, OSX/InfoStl-FR, and OSX/InfoStl-FH cover the known MacSync variants.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.