Security databases published 644 new CVEs on March 12, 2026, with 304 flagged as operationally relevant. Two scored a perfect CVSS 10.0. The first, CVE-2026-31957, affects Himmelblau, an open-source interoperability suite for Microsoft Azure Entra ID and Intune on Linux. The second, CVE-2026-31852, targets the Jellyfin iOS GitHub Actions workflow.
Himmelblau versions 3.0.0 through 3.0.x ship with an unscoped authentication mode when the tenant domain is not configured in himmelblau.conf. Without this setting, the system dynamically registers authentication providers at runtime for any Entra ID domain an attacker specifies. The result is cross-tenant authentication bypass, and in some configurations, privilege escalation through group-based role mappings.
No prior authentication to the Himmelblau instance is required.
A second Himmelblau flaw landed the same day. CVE-2026-31979 (CVSS 8.8) enables local privilege escalation to root through a symlink attack. The himmelblaud-tasks daemon writes Kerberos cache files under /tmp/krb5cc_ without symlink protection, and a prior commit (87a51ee) explicitly removed PrivateTmp from the daemon's systemd hardening. A local user can redirect the root-privileged write to any file on the system.
Himmelblau 3.1.0 is a security-focused release that fixes two high-impact vulnerabilities. All users are strongly encouraged to upgrade immediately.
— the Himmelblau project stated in its March 10 release notes on GitHub
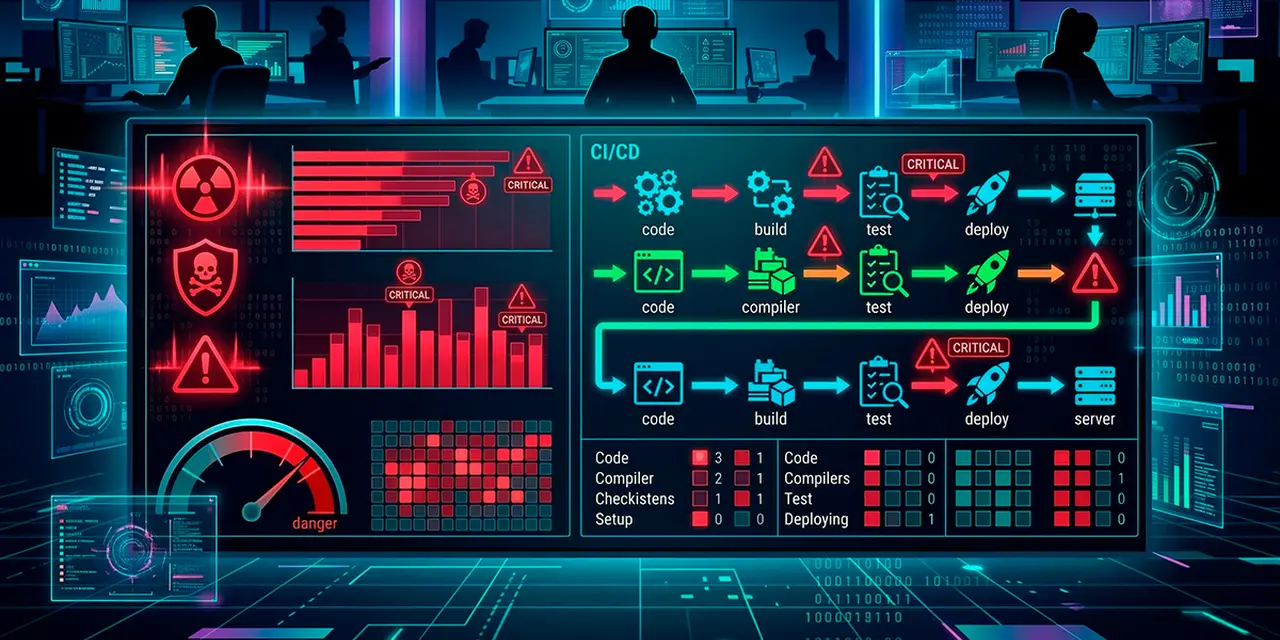
The Jellyfin CVSS 10 is a CI/CD (continuous integration/continuous delivery) workflow vulnerability, not a code flaw. The code-quality.yml GitHub Actions workflow in jellyfin/jellyfin-ios accepted pull requests from forked repositories with nearly all write permissions. An attacker could achieve full repository takeover, exfiltrate Apple App Store deployment secrets, poison GitHub Container Registry packages, and compromise the entire Jellyfin organization through cross-repository token reuse.
This is not a code vulnerability, but a vulnerability in the GitHub Actions workflows. No new version is required and end users do not need to take any actions.
— the Jellyfin advisory (GHSA-7qhm-2m45-7fmh) stated.
Parse Server drew a critical SQL injection. CVE-2026-31871 (CVSS 9.3) affects the PostgreSQL storage adapter when processing Increment operations on nested object fields using dot notation (e.g., stats.counter). The sub-key name is interpolated directly into SQL string literals without escaping. All Parse Server versions before 8.6.31 and 9.x versions before 9.6.0-alpha.5 are vulnerable. No authentication is required. Parse Server has a history of PostgreSQL adapter injection flaws, with CVE-2024-39309 (also SQL injection via regex) patched in July 2024.
| CVE | CVSS | Product | Fix |
|---|---|---|---|
| CVE-2026-31957 | 10.0 | Himmelblau (Azure Entra ID) | 3.1.0 |
| CVE-2026-31852 | 10.0 | Jellyfin iOS (CI/CD workflow) | Commit 109217e |
| CVE-2026-31871 | 9.3 | Parse Server (PostgreSQL) | 8.6.31 / 9.6.0-alpha.5 |
| CVE-2026-31979 | 8.8 | Himmelblau (symlink LPE) | 3.1.0 / 2.3.8 |
| CVE-2025-68623 | 8.8 | DirectX Runtime Web Installer | Pending |
| CVE-2026-22572 | 7.2 | Fortinet FortiAnalyzer | Pending |
Jellyfin and Xygeni both fell to CI/CD pipeline attacks the same week. The Xygeni tag poisoning (March 3 to 10) and the Jellyfin workflow vulnerability both exploit mutable references and overprivileged GitHub Actions to achieve supply chain compromise. Unlike traditional code vulnerabilities, these flaws live in CI/CD configuration files and do not require a software update for end users.
Some March 12 CVEs had already appeared in databases a day earlier. CVE-2026-0953 (Tutor LMS Pro authentication bypass, CVSS 9.8, patched in 3.9.6), CVE-2026-28495 (GetSimple CMS CSRF-to-RCE, CVSS 9.6), and CVE-2026-3843 (BUK TS-G gas station SQL injection, CVSS 9.3) remain active. Readers running those products should refer to our earlier coverage for full details and patching guidance.
Organizations running Himmelblau for Azure Entra ID integration should update to version 3.1.0 immediately and verify that a tenant domain is explicitly configured in himmelblau.conf. Parse Server operators on PostgreSQL should upgrade to 8.6.31 or 9.6.0-alpha.5. Teams managing GitHub Actions workflows should audit write permissions on workflows triggered by pull requests from forks.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







