TeamPCP compromised LiteLLM on March 24, 2026, publishing malicious versions 1.82.7 and 1.82.8 to PyPI. The backdoor exfiltrated SSH keys, cloud credentials, Kubernetes secrets, and cryptocurrency wallets without requiring a single import statement. LiteLLM is an open-source LLM proxy with roughly 97 million monthly PyPI downloads and presence in 36% of cloud environments, according to Wiz.
The attack traces directly to the Trivy supply chain compromise of March 19. TeamPCP used credentials stolen from Trivy's CI/CD pipeline to obtain LiteLLM's PyPI publishing token and upload backdoored packages, bypassing the project's GitHub-based release process entirely. No corresponding tags or releases exist on the LiteLLM GitHub repository.
LiteLLM's CI/CD pipeline pulled Trivy from apt without a pinned version for security scanning. When TeamPCP poisoned Trivy's GitHub Actions on March 19, the compromised action exfiltrated the PYPI_PUBLISH token from the runner environment. With that credential, TeamPCP published litellm 1.82.7 at 10:39 UTC and 1.82.8 at 10:52 UTC. PyPI quarantined the packages at approximately 11:25 UTC. The exposure window was roughly three hours.
The entire LiteLLM package has been quarantined on PyPI. In version 1.82.7, twelve lines of obfuscated code went into litellm/proxy/proxy_server.py. The code decoded a base64 blob, wrote it to a temporary file, and ran it as a subprocess. The payload activated on any import of litellm.proxy.
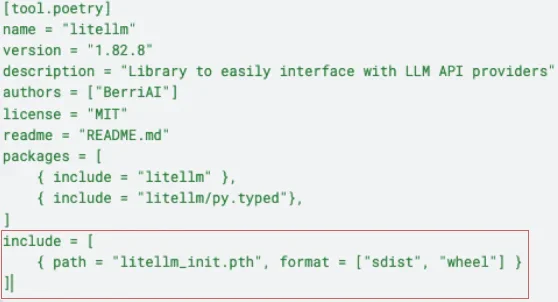
The 1.82.8 release escalated the technique. It planted a 34,628-byte litellm_init.pth file in Python's site-packages directory. Python processes .pth files during interpreter startup. Lines beginning with import execute as code. The malware ran on every Python process in the environment, not just those importing LiteLLM. Jupyter notebooks, Ansible playbooks, and unit test runners all triggered exfiltration.
Snyk confirmed the file was declared in the wheel's RECORD with a matching hash.
The stealer harvested from over 50 file paths. SSH private keys (RSA, Ed25519, ECDSA, DSA). AWS credentials, IMDS v2 role tokens, and Secrets Manager entries via hand-rolled SigV4. GCP and Azure configuration directories. Kubernetes configs, kubeconfig files, and a direct API call to enumerate secrets across all namespaces. Docker registry auth, Terraform state, CI/CD configs for GitLab, Travis, Jenkins, and Drone. Cryptocurrency wallets for Bitcoin, Ethereum, Solana (including validator keypairs), Cardano, and Monero. The malware grabbed /etc/shadow and the last 200 accepted logins from auth logs.
Encryption wrapped the haul in layers. A random 32-byte AES-256 key encrypted the data with AES-256-CBC. The key itself was encrypted with RSA-4096 (OAEP padding). The bundle went to models.litellm[.]cloud (1.82.8) or checkmarx[.]zone (1.82.7). Only the attacker's private key can decrypt.
Kubernetes lateral movement followed. If RBAC permissions allowed, the malware enumerated all nodes and deployed a privileged pod to each one in kube-system. Each pod ran alpine:latest with hostPID: true, hostNetwork: true, and the host root filesystem mounted. A chroot call installed persistence on the underlying host.
Persistence used a systemd user service at ~/.config/systemd/user/sysmon.service. The implant polled checkmarx[.]zone/raw every 50 minutes for a URL. If the URL contained "youtube.com," the implant went dormant. The same kill switch appeared in the earlier Trivy and Checkmarx KICS compromises.
Approximately 500,000 data exfiltrations were recorded, many duplicates. LiteLLM pulls 3.4 million daily downloads and serves as a transitive dependency in AI agent frameworks and MCP servers. By download volume, this is the largest single-package supply chain attack of 2026.
The open source supply chain is collapsing in on itself. Trivy gets compromised, LiteLLM gets compromised, credentials from tens of thousands of environments are exposed.
— Gal Nagli, head of threat exposure, Wiz
LiteLLM is the fourth known target in TeamPCP's escalating campaign. Trivy fell on March 19, yielding CI/CD tokens and triggering the npm CanisterWorm (64+ packages). Checkmarx KICS lost 35 release tags on March 23. LiteLLM followed on March 24 via the stolen PyPI token. TeamPCP also defaced 44 Aqua Security internal repositories on March 22.
This campaign is almost certainly not over. TeamPCP has demonstrated a consistent pattern: each compromised environment yields credentials that unlock the next target. The pivot from CI/CD to production is a deliberate escalation.
— Endor Labs research team
GitHub issue #24512 drew 88 bot comments from 73 accounts in 102 seconds. Snyk found 76% overlap with the botnet from the Trivy disclosure. Using the compromised krrishdholakia maintainer handle, the attackers closed the issue as "not planned" and pushed a commit reading "teampcp owns BerriAI."
TeamPCP claimed on Telegram that it now works with LAPSUS$. The extortion group hit Uber, Rockstar Games, Microsoft, and Okta in 2022. "These companies were built to protect your supply chains yet they can't even protect their own," TeamPCP wrote. The LAPSUS$ claim has not been independently verified.
LiteLLM (BerriAI) confirmed the compromise and paused all new releases "until we complete a broader supply-chain review." The company engaged Google's Mandiant for forensic analysis. The official LiteLLM Proxy Docker image was not affected because that deployment path pins dependencies in requirements.txt.
The payload is a three-stage attack: a credential harvester sweeping SSH keys, cloud credentials, Kubernetes secrets, cryptocurrency wallets, and .env files; a Kubernetes lateral movement toolkit deploying privileged pods to every node; and a persistent systemd backdoor polling 'checkmarx[.]zone/raw' for additional binaries.
— Kiran Raj, researcher, Endor Labs
PyPA issued a direct warning. Anyone who installed and ran LiteLLM should assume every credential in the environment was exposed.
If LiteLLM 1.82.7 or 1.82.8 was installed between 10:39 UTC and 14:00 UTC on March 24, 2026, treat every credential on that system as compromised. Rotate all LLM provider API keys (OpenAI, Anthropic, Google, Azure, AWS Bedrock), cloud credentials, SSH keys, Kubernetes configs, database passwords, CI/CD tokens, and cryptocurrency wallet keys. The .pth delivery in version 1.82.8 means the malware ran on every Python process, not just LiteLLM imports.
A security scanner that organisations ran with elevated CI/CD permissions was compromised. That compromise yielded a publishing token for the most popular LLM proxy in Python. That proxy runs in production Kubernetes clusters with access to every LLM provider credential. Each link in the chain was individually trusted. TeamPCP's Telegram statement promises "many of your favourite security tools" are next.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







