A threat actor using the alias "korea" has published the full database of OptimizerAI, a US-based AI sound effects generator, on an underground forum. The dump contains 118,000 unique user records and more than 1.1 million AI-generated audio files. According to the forum post, the breach occurred in February 2026; the data appeared for free download on March 3.
OptimizerAI (optimizerai.xyz) turns text prompts into sound effects, type "futuristic gun blast" or "deep dragon growl," and the neural network produces audio. Subscriptions start at $3 per month. The platform's audience is mostly indie game developers, animators, and video editors. According to PitchBook, OptimizerAI raised $500,000 in funding from Andreessen Horowitz, Capstone Partners Korea, and Krew Capital, making it a small but venture-backed startup.
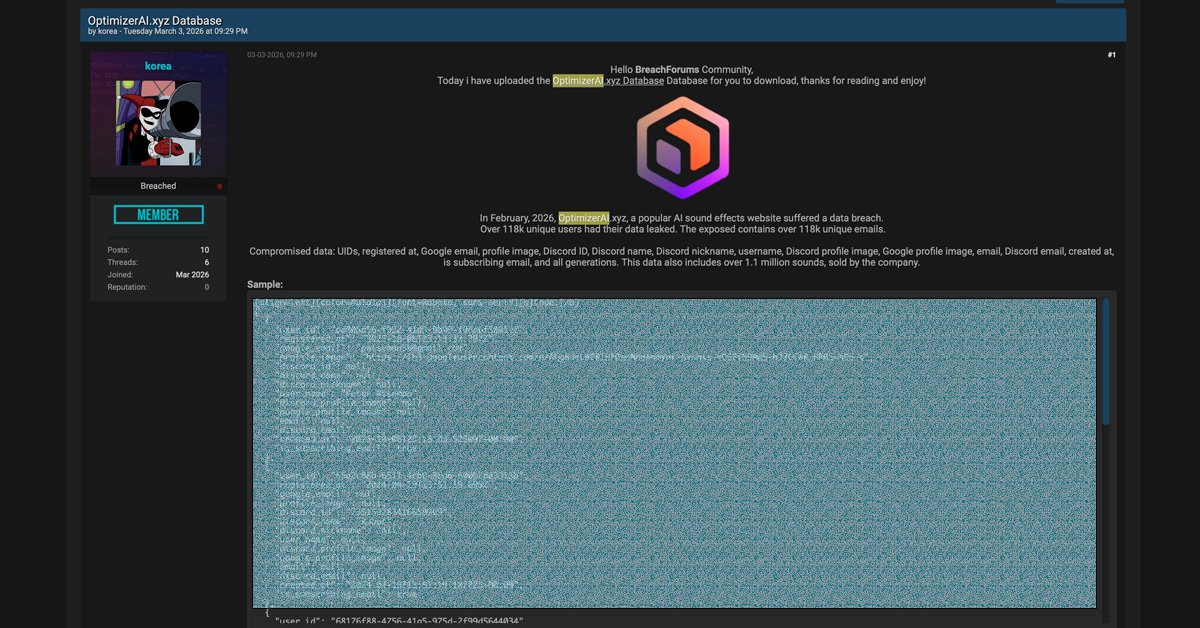
What makes this breach unusual is the cross-platform profile linking. The dump ties together each user's Google account and Discord identity in a single record: Google email addresses, Google UIDs, Google avatars, Discord IDs, Discord usernames (display name, nickname, and handle), Discord avatars, Discord email addresses, registration dates, and newsletter subscription status. OptimizerAI integrates deeply with Discord, letting users generate sounds directly in chat, which means most accounts carried both identities.
That pairing is the real damage. Discord usernames often serve as gaming handles or pseudonyms, and tying them to a real-name Google email strips away anonymity. For anyone who kept their Discord identity separate from their professional life, that wall is gone. DarkWebInformer, which first reported the breach, classified it as a medium-severity incident. According to the site's assessment, the threat actor "korea" posted the data for free, no sale price, just a requirement to leave a forum comment before downloading, as a reputation-building exercise rather than a profit-driven operation.
The 1.1 million audio files add a second dimension. According to the forum post, OptimizerAI sold these files commercially as royalty-free sound effects. Publishing the entire library for free undercuts the subscription model that the platform's paying users supported. Whether the files carry individual copyright to their creators or to OptimizerAI depends on the platform's terms of service, but either way, the commercial value of the catalog dropped to zero the moment it hit the forum.
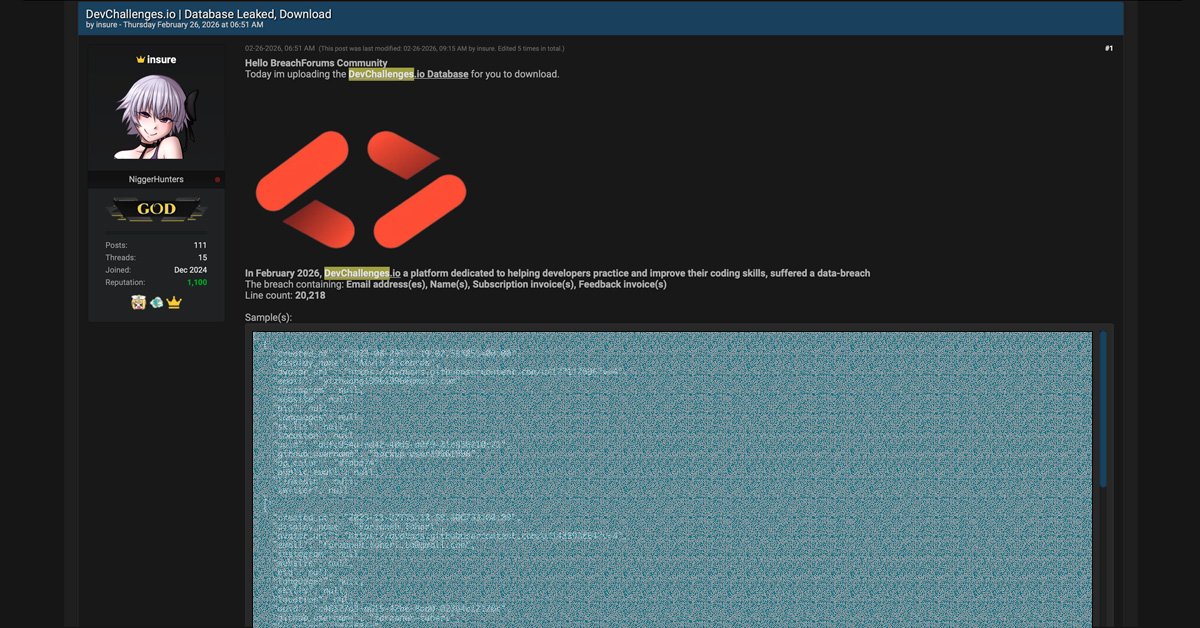
Cross-platform identity leaks like this are becoming a pattern. In February 2026, a separate threat actor published the DevChallenges database, 20,218 records linking email addresses, GitHub profiles, and user data, for free download on a similar forum, according to DarkWebInformer. A month earlier, in January 2026, the HawkSec group claimed to have obtained 78 million Discord-related records (though researchers at Cybernews questioned those claims because no public sample was provided). Discord itself disclosed a third-party breach in late 2025 that exposed government-issued IDs and personal details of users who had contacted its support team. Small platforms that piggyback on Discord for authentication are creating secondary exposure channels, if the platform gets breached, the Discord profile goes with it.
OptimizerAI has not commented on the incident. The site at optimizerai.xyz remained operational as of March 5, 2026, with no visible breach notification or status update.
Users who authenticated with OptimizerAI through Google or Discord should review active sessions in both services and revoke any unfamiliar access. If the Discord password matched credentials on other platforms, it should be changed. Enabling two-factor authentication in Discord (Settings → My Account → Two-Factor Authentication) blocks the most direct attack path from stolen credentials.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.