
Perseus, a new Android banking trojan, opens note-taking apps and reads their contents. ThreatFabric disclosed the malware on March 19, 2026. Perseus targets 42+ financial institutions and nine cryptocurrency services across Turkey (17 banks), Italy (15), Poland (5), Germany (3), France (2), the UAE, and Portugal.
The name comes directly from the C2 login panel ThreatFabric accessed during campaign analysis.
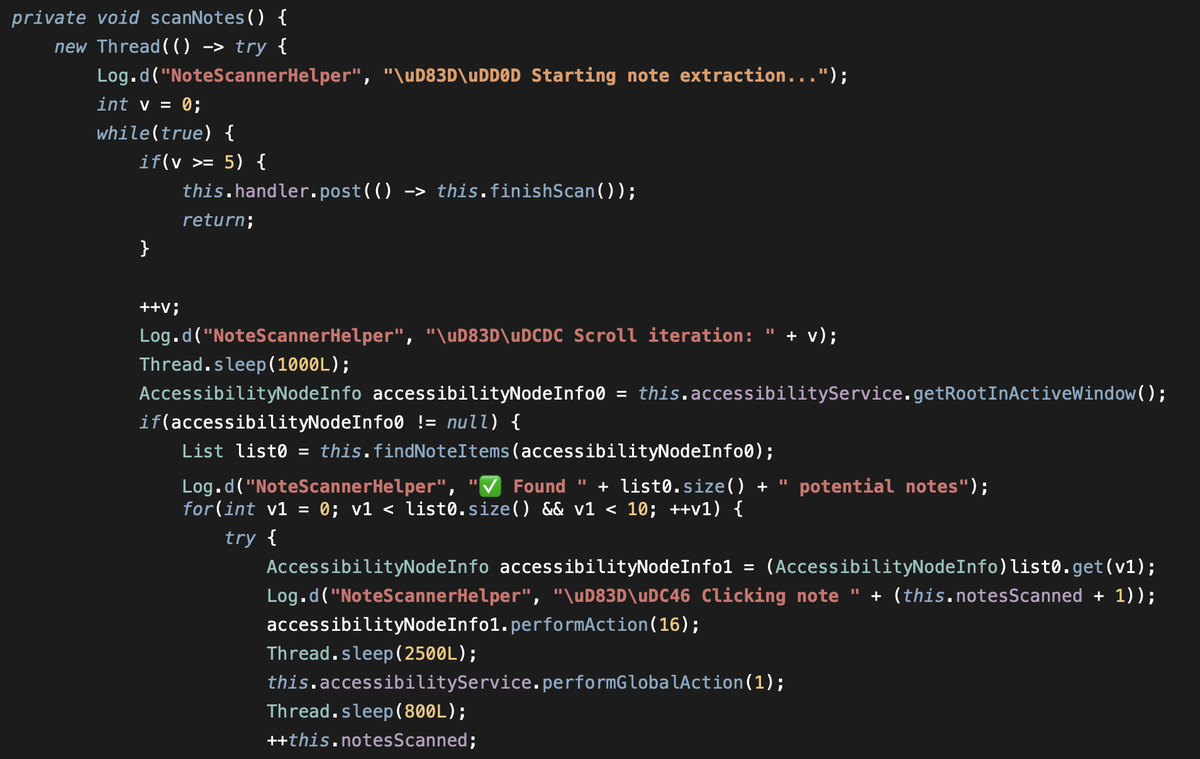
The defining feature is a command called scan_notes. It uses Android Accessibility Services to open seven note-taking apps one by one, navigate entries, and exfiltrate contents to the C2 server. The list includes Google Keep, Xiaomi Notes, Samsung Notes, ColorNote, Evernote, and Simple Notes Pro. Microsoft OneNote is on the list too, though ThreatFabric found a wrong package name that likely breaks that scan.
While many Android malware families focus primarily on harvesting credentials or intercepting communications, this feature reflects a broader interest in contextual and personally curated data. Notes often contain sensitive information such as passwords, recovery phrases, financial details, or private thoughts, making them a valuable target for attackers.
— ThreatFabric
Perseus targets the data people assume is safe. Seed phrases for crypto wallets, 2FA backup codes, PINs jotted as reminders, emergency passwords stored in Keep or Samsung Notes.
Thirty-five operator commands round out the toolkit. Continuous screenshot streaming (start_vnc) and a JSON UI skeleton for programmatic control (start_hvnc) give the operator real-time device takeover. Overlay attacks place fake login screens over banking apps.
One command (get_unlockpass) steals the device unlock credential. Another (action_set_clipboard) replaces clipboard contents with operator text, a technique for swapping wallet addresses mid-transaction. A black screen overlay hides activity from the victim. The modular architecture lets operators add or remove capabilities on the fly.
Perseus builds on the Phoenix codebase, itself a fork of Cerberus. ThreatFabric first documented Cerberus in August 2019. Its source code leaked on underground forums in 2020 after a failed auction, spawning Alien, ERMAC, Hook, Octo, and Phoenix. Two Perseus variants exist. The Turkish-language version came first. The English-language variant is more refined, with better debugging, extensive in-app logging, and emojis in the source code. ThreatFabric interprets the emoji-laden comments as a signal that LLMs assisted in development.
Distribution runs through fake IPTV (Internet Protocol Television) apps on unofficial stores and phishing sites. One identified dropper is called "Roja App Directa," mimicking the popular (and legally contested) sports streaming service Roja Directa. Users seeking pirated football streams already expect to sideload APKs, dismiss Android warnings, and grant broad permissions. The dropper bypasses Android 13+ sideloading restrictions. The same dropper infrastructure delivers Klopatra and Medusa, two other banking trojans with European targeting.
By embedding its payload within this expected context, the Perseus malware effectively reduces user suspicion and increases infection success rates, blending malicious activity with a commonly accepted distribution model for such services.
— ThreatFabric
Before executing, Perseus runs a "suspicion score" system. It checks for root access, Frida instrumentation, debugger attachment, and emulator fingerprints. It also verifies SIM card presence, hardware profile consistency, battery data, Bluetooth adapter, installed app count, and Play Services. All results combine into a numerical score sent to the C2 panel. The operator decides whether to proceed.
IPTV-themed Android malware is a sustained distribution pattern. In February 2026, ThreatFabric documented Massiv, another banking trojan spread through fake IPTV apps targeting Portugal, Greece, Spain, France, and Turkey. Most IPTV campaigns over the past eight months have focused on Southern and Western Europe, driven by demand for free football broadcasts.
Cleafy documented Klopatra in September 2025 with indicators pointing to a Turkish-speaking development group. The IPTV distribution, European banking targets, and Turkey-focused primary variant suggest Perseus comes from the same community.
Perseus is not available on the Play Store. Play Protect should detect known samples if enabled. ThreatFabric published three IOC hashes. The installer (com.xcvuc.ocnsxn, "Roja App Directa") carries SHA-256 1ea8360c…29bdda. The English payload (com.tvtapps.live, "TvTApp") is 2524e9d5…b3529a. The Turkish payload (com.streamview.players, "PolBox Tv") is 56d3bb5e…f87093d.
Avoid sideloading APKs from unofficial sources, especially IPTV and sports streaming apps. Move passwords, crypto recovery phrases, and 2FA backup codes out of note-taking apps and into a dedicated password manager or hardware-based storage. Any data stored in Keep, Samsung Notes, Evernote, or similar apps is accessible to malware with Accessibility permissions.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







