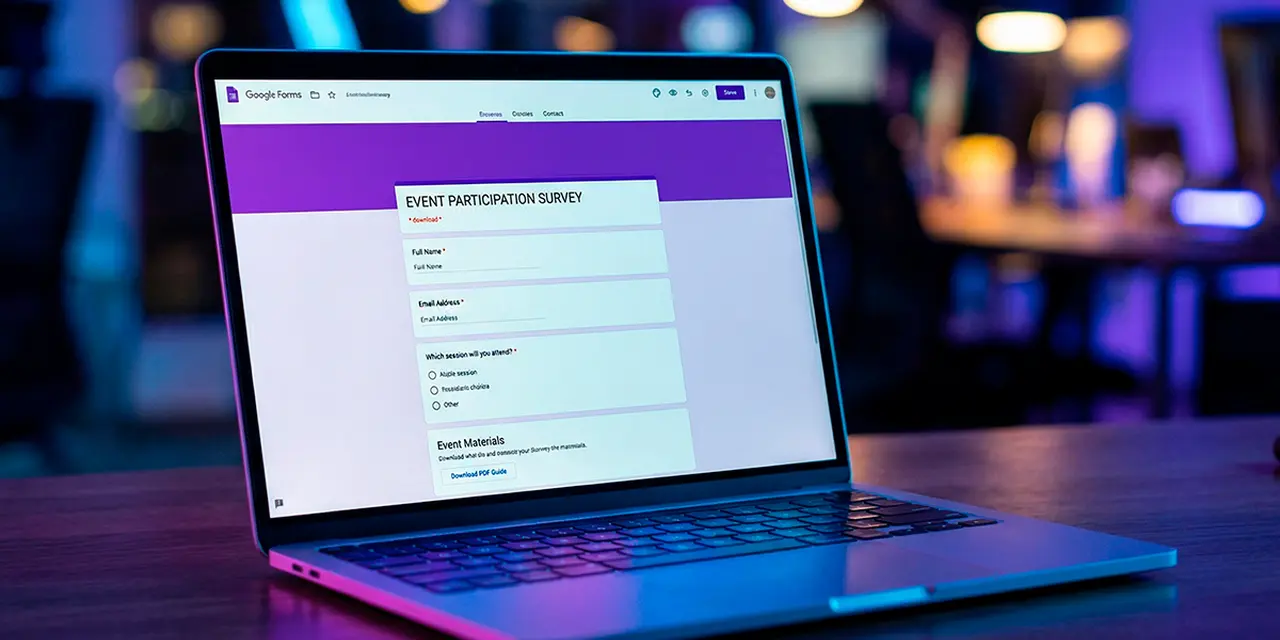
Fake job interviews on Google Forms are installing the PureHVNC remote access trojan. Malwarebytes researcher Gabriele Orini reported the campaign on March 20, 2026. The forms impersonate real companies in finance, logistics, technology, sustainability, and energy. Victims who download ZIP archives linked from the forms trigger a multi-stage infection chain that ends with full remote control.
Google Forms is what makes this operation different from standard phishing. The forms live on docs.google.com, a domain that bypasses email security gateways, URL reputation filters, and user suspicion in one move. The payload never touches the form itself. It sits on Dropbox, filedn.com, or fshare.vn, reachable only after the victim has already engaged with what looks like a legitimate Google product.
LinkedIn is one of the platforms used to distribute links to the weaponized forms, according to Malwarebytes. The forms ask for professional information (work experience, qualifications, background) and carry correct logos and branding of the impersonated companies. URL shorteners (tr.ee, goo.su) and Google redirect links obscure the final download destination.
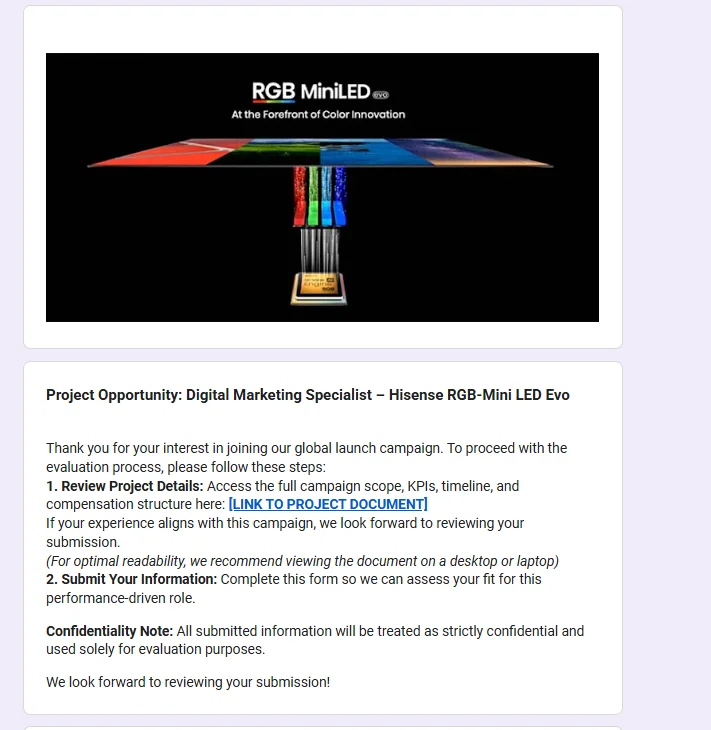
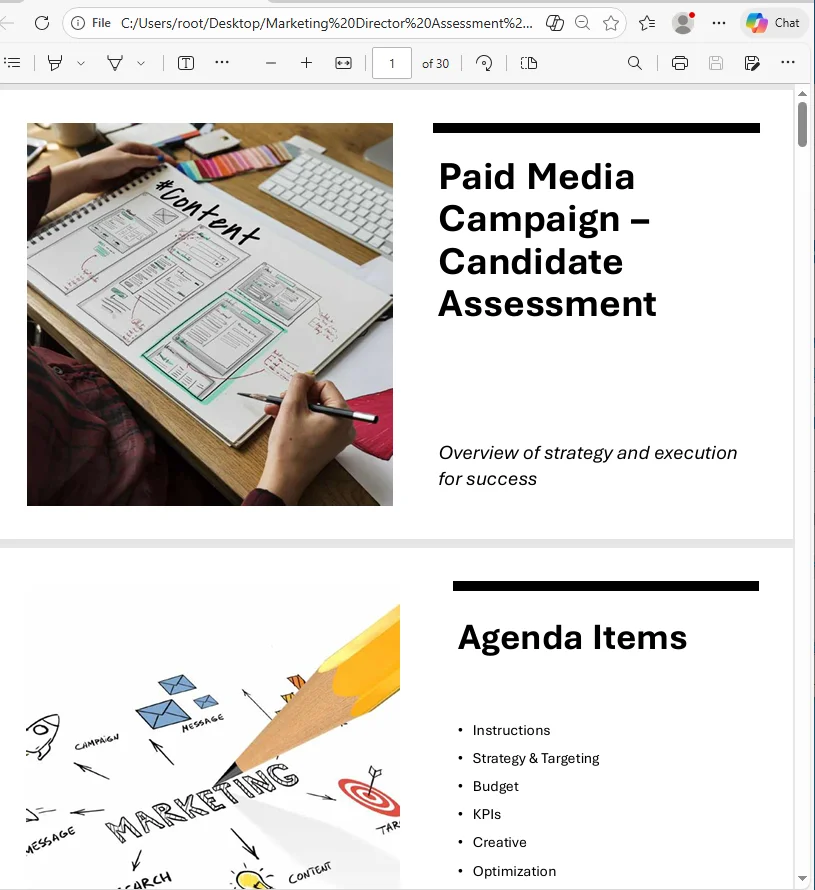
ZIP file names follow business themes. Malwarebytes listed examples including {CompanyName}_GlobalLogistics_Ad_Strategy.zip, Project_Information_Summary_2026.zip, and {CompanyName}_Company_and_Job_Overview.pdf.rar.
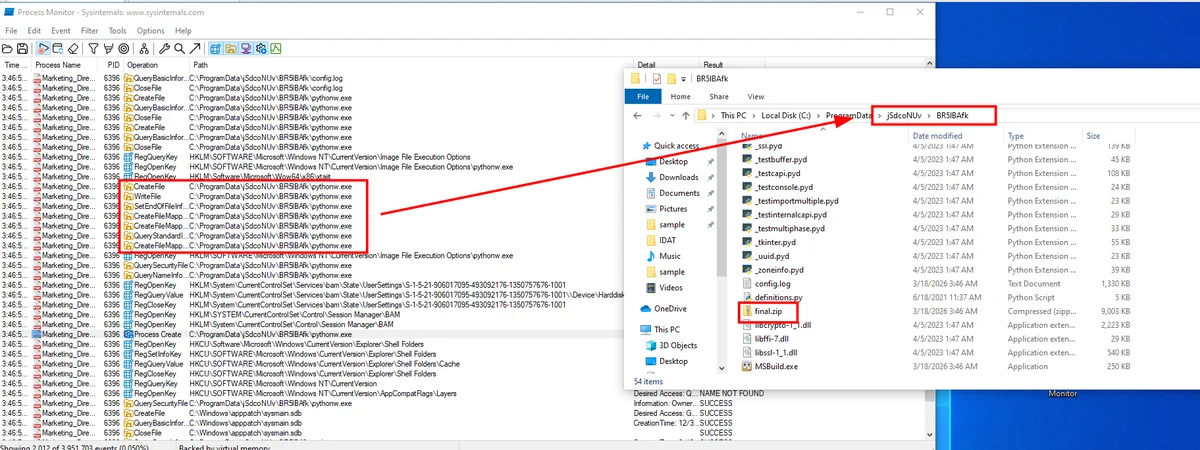
DLL hijacking drives the infection chain. Each ZIP archive Malwarebytes analyzed contains legitimate PDFs alongside an executable and a DLL named msimg32.dll. The executable loads the DLL on launch.
Once loaded, msimg32.dll decrypts strings with XOR key "4B". It runs anti-analysis checks via the Windows API calls IsDebuggerPresent() and time64(). If triggered, it displays "This software has expired or debugger detected." Otherwise it deletes itself and opens a decoy PDF to maintain the business illusion.
Persistence comes through the registry key CurrentVersion\Run\Miroupdate. The DLL extracts an archive called final.zip into a random folder under ProgramData using the tar command. Inside are Python files and the next stage. An obfuscated Python script (disguised as config.log or image.mp3) decodes and executes Donut shellcode, which injects PureHVNC into SearchUI.exe.
It's not the malware that's new, but how the attack starts. Instead of the usual phishing email or fake download page, attackers are using Google Forms to kick off the infection chain.
— Gabriele Orini, threat intelligence researcher, Malwarebytes
PureHVNC belongs to the "Pure" family, a modular .NET RAT suite. The developer behind it, PureCoder, sells tools through underground forums and Telegram. Check Point researcher Antonis Terefos traced PureCoder's GitHub accounts in September 2025. All commits fell in the UTC+0300 timezone, consistent with Moscow, Minsk, or Istanbul. Netresec confirmed in August 2025 that PureHVNC, PureRAT, and ResolverRAT are names different vendors use for the same family.
The PureCoder toolkit extends beyond PureHVNC. PureRAT is the current-generation successor. PureCrypter obfuscates payloads, PureLogs steals credentials, PureMiner mines cryptocurrency, and PureClipper swaps crypto wallet addresses in the clipboard.
PureHVNC profiles the target through WMI queries after installation. It enumerates antivirus products (AntiVirusProduct), cameras (Win32_PnPEntity with PNPClass = 'Camera'), and OS details. It steals browser data from Chrome, Edge, Firefox, Internet Explorer, and 360 Browser. It targets cryptocurrency wallets and extracts data from Telegram and Foxmail. Persistence escalates to scheduled tasks with -RunLevel Highest if admin rights are available.
The analyzed sample's C2 sits at IP 207.148.66.14 on ports 56001, 56002, and 56003. Campaign ID is "Default" and the mutex is "Rluukgz". These port numbers and the base64+GZIP encoding match every known PureHVNC deployment since mid-2024.
Malwarebytes identified multiple variants with different extraction methods, Python code structures, and folder layouts.
PureHVNC has surfaced in at least five distinct campaigns since 2024. Fortinet documented a Python multi-stage loader in August 2024. Vietnamese-speaking operators promoted fake AI websites through Facebook malvertising, according to PCRisk. Check Point's September 2025 investigation followed a ClickFix campaign with fake job listings.
IBM X-Force tracked phishing targeting Colombian users via spoofed Attorney General documents between August and October 2025. Fortinet separately reported SVG-based phishing aimed at Ukraine and Vietnam that same month. The Google Forms vector is the latest evolution in delivery.
Google Forms does not appear to have removed the forms at the time of Malwarebytes' publication. Malwarebytes Browser Guard blocks the associated domains.
Malwarebytes published 20 file hashes and the C2 IP as indicators of compromise. ZIP archives containing both PDF documents and executables or DLLs (particularly msimg32.dll) are a red flag. No law enforcement action has been announced. Verify any Google Form requesting professional information and linking to downloadable archives through official company channels before engaging.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







