
Cybercriminals have turned Telegram into their main workspace, using the messenger to sell stolen corporate credentials, distribute malware, and coordinate attacks with a speed and resilience that traditional darknet forums never offered. Cyfirma, a threat intelligence firm, published an analysis on February 26, 2026, documenting how the platform now hosts nearly every stage of the criminal supply chain, from credential theft to ransomware deployment.
For years, Tor-based marketplaces like Hydra Market and RaidForums served as the backbone of the cybercriminal underground. They relied on reputation systems, escrow mechanisms, and invitation-only access. That structure made them organized but fragile: when law enforcement seized a forum, its entire ecosystem collapsed overnight. Telegram removed that single point of failure. If a channel gets blocked, the operator recreates it in minutes and redirects subscribers through forwarding links. Downtime is measured in hours, not months.
Cyfirma describes the shift as a "platformization of cybercrime." Criminal services increasingly mirror legitimate SaaS businesses, complete with subscriptions, automated delivery, product updates, and customer support. Launching an attack no longer requires programming skills. A Telegram account and a modest budget are enough to buy access to compromised networks, rent malware, or commission a DDoS campaign.
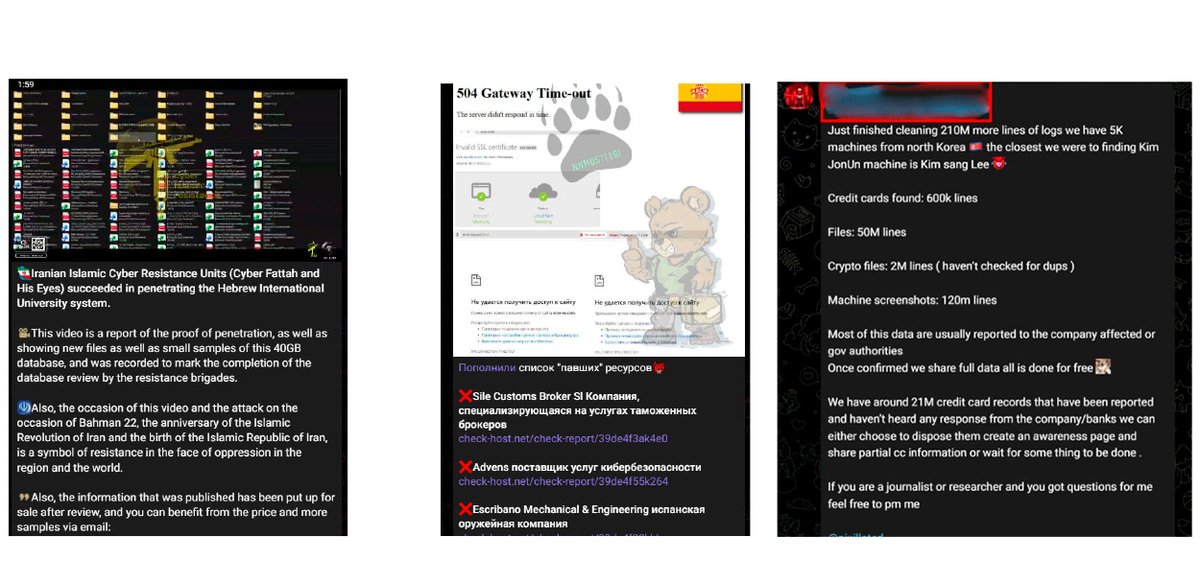
The most direct threat to enterprises comes from Initial Access Brokers (IABs), operators who specialize in selling verified entry points into corporate environments. Dedicated Telegram channels advertise stolen VPN credentials, Remote Desktop Protocol sessions, and access to cloud platforms such as Microsoft Azure, AWS, and Okta. Listings typically include the target company's revenue, country, industry, and privilege level, giving ransomware buyers everything they need to evaluate a purchase before committing. Sellers demonstrate live access in private chats, showing proof of RDP logins or cloud console visibility. According to Cyfirma, infostealers harvested an estimated 1.8 billion credentials in the first half of 2025, feeding the pipeline that IABs depend on. Automated bots extend the marketplace further. Some let buyers search leaked credential databases directly inside Telegram. Certain infostealer strains are configured to exfiltrate stolen data straight to Telegram bots via the messenger's API, eliminating the need for separate command-and-control infrastructure. Malware-as-a-Service operators manage their entire business on the platform: marketing new builds, pushing updates to subscribers, and handling support tickets through group chats.
Telegram's role goes beyond commerce. Hacktivist groups coordinate DDoS attacks and amplify propaganda through public channels. Cyfirma names NoName057(16) and Cyber Fattah Team as groups that use the messenger simultaneously for operational command and information warfare. Ransomware gangs publish countdown timers and fragments of stolen data in their channels, increasing psychological pressure on victims who refuse to pay.
The trend is not new, but its scale has accelerated. Kaspersky's Digital Footprint Intelligence team measured a 53% surge in cybercrime-related posts on Telegram between May and June 2024, compared to the same period a year earlier. Alexey Bannikov, a Kaspersky analyst, attributed the growth to Telegram's 900-million-strong user base, its reputation as a privacy-focused platform, and the ease of creating communities. A UNODC report published in October 2024 reached similar conclusions, finding strong evidence that underground data markets were migrating to Telegram, particularly among organized crime networks in Southeast Asia that generate between $27.4 billion and $36.5 billion annually in fraud revenue.
Cyfirma warns that the convergence of credential theft, access brokerage, and ransomware operations on a single platform has compressed attack timelines. In some cases, stolen credentials appear on Telegram and lead to ransomware deployment in under 48 hours. Traditional dark web intelligence methods struggle to track threats that now move through encrypted group chats and disposable channels rather than indexed forum threads.
The dark web has not disappeared. Tor-based forums still host initial negotiations and serve as reputation anchors for established vendors. But the operational center of gravity has shifted. Telegram functions as a faster, more accessible extension of the underground, one that runs on a mainstream app installed on hundreds of millions of phones.
Enterprise defenders who limit their threat monitoring to traditional dark web sources risk missing the channels where stolen credentials and network access are actively traded. Extending intelligence coverage to Telegram, auditing exposed credentials, enforcing phishing-resistant MFA, and removing unnecessary RDP exposure are the immediate steps that reduce the attack surface IABs depend on.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.




