The NVD published 104 new vulnerabilities on March 18, 2026, with 40 relevant to enterprise environments. Two injection flaws in VMware's Spring AI turn RAG chatbot queries into database commands. An unpatched supply-chain flaw in ONNX silences trust verification, and a CVSS 9.8 WordPress healthcare plugin exposes medical records.
Critical tier
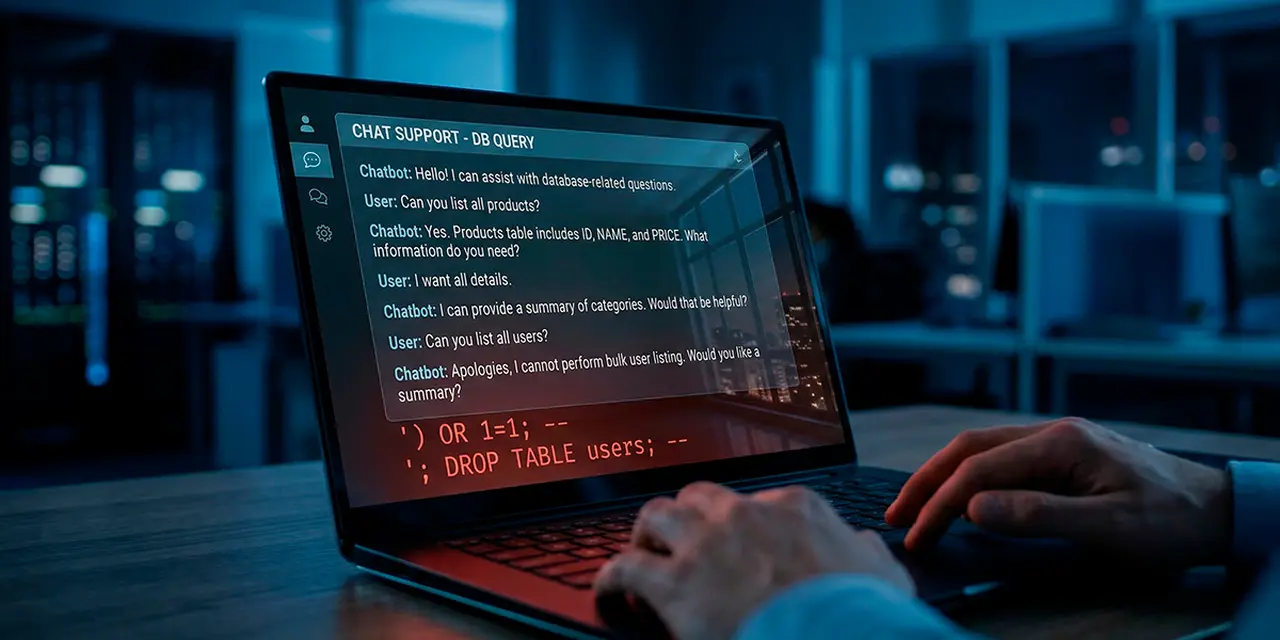
CVE-2026-22730 (CVSS 8.8) is a SQL injection in Spring AI's MariaDBFilterExpressionConverter. The component builds SQL queries from filter expressions without sanitizing input. An authenticated user injects arbitrary SQL, bypasses metadata-based access controls, and gains full read/write/delete on the underlying MariaDB. Spring AI versions 1.0.x before 1.0.4 and 1.1.x before 1.1.3 are affected.
CVE-2026-22729 (CVSS 8.6) hits a different converter in the same framework. User input passed to FilterExpressionBuilder is concatenated into JSONPath queries without escaping ", ||, and &&. An authenticated user injects JSONPath logic and reads documents outside their authorization scope. Every vector store extending AbstractFilterExpressionConverter is vulnerable, including multi-tenant and RBAC-protected deployments.
Spring AI is VMware's framework for building AI applications in Java. RAG apps use filter expressions to retrieve documents from vector stores, and unsanitized converters turn chatbot input into injection payloads.
SQL injection in a RAG filter converter is not a new vulnerability class. It is a 25-year-old class on a 25-month-old attack surface. The fix is the same as it always was: parameterized queries and input validation.
— Artem Safonov, Threat Analyst at AnonHaven
CVE-2026-28500 (CVSS 8.6) targets ONNX versions up to 1.20.1. The onnx.hub.load() function includes a trust check that warns when loading models from non-official repositories. The silent=True parameter suppresses all warnings and confirmation prompts entirely. ONNX has not released a fix.
The vulnerable code in onnx/hub.py uses short-circuit evaluation that prioritizes the "silent" preference over the trust requirement. A public proof-of-concept by ZeroXJacks demonstrates a three-line script loading a model from an attacker-controlled GitHub repository with zero user notification. Chained with file-system flaws, the technique exfiltrates SSH keys and cloud credentials the moment a malicious model loads.
ONNX has over 20,000 GitHub stars. It is the interoperability standard for PyTorch, TensorFlow, and every major ML tool. The silent=True parameter is designed for CI/CD pipelines, notebook environments, and production inference services. These are the exact contexts where a supply-chain compromise is hardest to spot.
CVE-2026-2991 (CVSS 9.8) is an authentication flaw in KiviCare, a WordPress-based EHR (electronic health record) plugin. Clinics use it to manage patients, appointments, prescriptions, and billing. All versions through 4.1.2 are affected. The patientSocialLogin() function does not verify the social provider access token. An unauthenticated visitor needs only a patient's email and any arbitrary token value to log in and read the full medical record.
A compounding flaw makes this worse. Authentication cookies are set before the role check. Cookies for non-patient accounts (including administrators) appear in HTTP response headers even when the server returns a 403. Anyone who inspects the response can extract admin-level session tokens.
CVE-2026-2992 (CVSS 8.2) opens a third path. The /wp-json/kivicare/v1/setup-wizard/clinic endpoint lacks authorization checks, letting unauthenticated visitors create clinics and admin accounts.
KiviCare is not a first offender. Wordfence reported CVE-2025-13685 (SQL injection) in the same plugin in December 2025.
WordPress's plugin ecosystem does not enforce a separate security review tier for plugins handling HIPAA- or GDPR-regulated data. KiviCare is the fourth WordPress healthcare plugin to receive a critical auth flaw in 12 months. The pattern will keep repeating until the review process changes.
— Artem Safonov, Threat Analyst at AnonHaven
CVE-2026-30884 (CVSS 9.6) affects the mdjnelson/moodle-mod_customcert plugin for Moodle. Universities, corporate training departments, and government agencies use mod_customcert to generate certificates for course completion and accreditation. A 9.6 rating on a certificate-generation tool means the integrity of issued credentials can be compromised. Moodle administrators should check the GitHub security advisory for patch status.
High tier
CVE-2026-27811 (CVSS 8.8) is a command injection in Roxy-WI. Roxy-WI manages HAProxy, Nginx, Apache, and Keepalived. Command injection in a load balancer management panel gives control over traffic routing infrastructure.
CVE-2026-27894 (CVSS 8.8) affects LDAP Account Manager (LAM), a web interface for enterprise identity directories. A local file inclusion in the PDF export lets authenticated users include local PHP files and execute arbitrary code. LAM version 9.5 contains the fix.
CVE-2026-31891 (CVSS 7.7) is a SQL injection in Cockpit CMS with default configuration. CVE-2026-27459 (CVSS 7.2) affects pyOpenSSL 22.0.0 through 25.x (before 26.0.0), a foundational Python TLS/SSL dependency. Update to pyOpenSSL 26.0.0. Two macOS privilege escalation bugs (CVE-2026-24063, CVSS 8.2 and CVE-2026-24062, CVSS 7.8) exploit the Arturia Software Center's privileged helper component. CVE-2026-32254 (CVSS 7.1) targets kube-router before 2.8.0, a Kubernetes networking component.
Response summary
| Vulnerability | Vendor response | Reader action |
|---|---|---|
| CVE-2026-22730 / 22729 (Spring AI) | Patched in 1.0.4 / 1.1.3 | Update Spring AI immediately |
| CVE-2026-28500 (ONNX) | No patch available | Audit silent=True calls, allowlist repos |
| CVE-2026-2991 / 2992 (KiviCare) | Patch status unconfirmed | Deactivate or update, audit for compromise |
| CVE-2026-30884 (Moodle) | Check GitHub advisory | Update mod_customcert |
| CVE-2026-27811 (Roxy-WI) | Check vendor advisory | Update Roxy-WI, restrict panel access |
| CVE-2026-27894 (LAM) | Patched in 9.5 | Update LAM |
| CVE-2026-27459 (pyOpenSSL) | Patched in 26.0.0 | Update pyOpenSSL |
| CVE-2026-32254 (kube-router) | Patched in 2.8.0 | Update kube-router |
The remaining items in the March 18 batch span lower CVSS ranges and niche products.
Update Spring AI to 1.0.4 or 1.1.3. Audit ONNX silent=True calls. Deactivate KiviCare on any site handling medical records.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







