198 new CVEs were published over the March 21-22, 2026 weekend. Of those, 119 affect enterprise and web infrastructure. Two reach Critical severity. A BACnet protocol flaw (CVSS 9.1) exposes building automation systems to traffic interception, and a seven-year-old Memu Play exploit (CVSS 9.3) finally received a CVE. WordPress plugin flaws dominate the rest of the batch, with at least 15 high-severity privilege escalation, SQL injection, and SSRF bugs.
Critical
BACnet service packets transmit unencrypted over the wire. CVE-2026-24060 (CVSS 9.1) affects building automation systems that use BACnet for HVAC, lighting, access control, and fire detection. An attacker on the same network segment can sniff, intercept, and modify service information. File Start Position and File Data are exposed in plaintext, readable with Wireshark's BACnet dissector.
The proprietary update format used by WebCTRL to receive PLC firmware can be reverse-engineered from captured traffic. Injecting crafted BACnet packets could disrupt or manipulate industrial processes. No authentication is required. The flaw is a protocol-level design oversight, not a software bug with a patch.
Memu Play 6.0.7 has a local privilege escalation to NT AUTHORITY\SYSTEM. CVE-2019-25568 (CVSS 9.3) allows any low-privilege user to replace MemuService.exe in the installation directory because the Everyone group has full control (icacls shows Everyone:(I)(F)). The service runs as Local System and auto-starts on reboot. A public exploit has been on Exploit-DB since February 2019. The formal CVE assignment arrived seven years later.
High
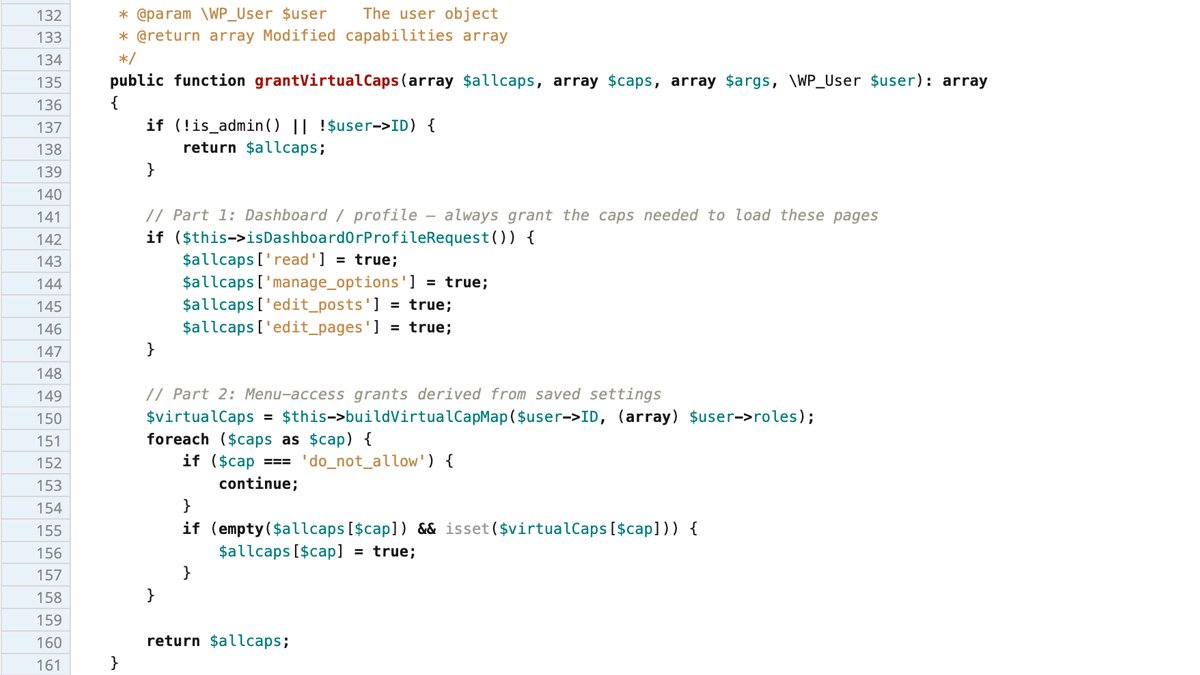
WP Extended ("The Ultimate WordPress Toolkit") ≤3.2.4 lets any subscriber become an administrator. CVE-2026-4314 (CVSS 8.8) sits in the Menu Editor module. The isDashboardOrProfileRequest() method uses PHP's strpos() to check the URI for dashboard paths.
The grantVirtualCaps() method, hooked into WordPress's user_has_cap filter, grants manage_options (full admin control) whenever that check passes. A subscriber appends ?page=wp-admin/profile.php to any admin URL. This satisfies strpos() without changing the request destination. The method grants full administrator capabilities for that single request. Wordfence disclosed the flaw and a patch is available via WordPress plugin trac changeset.
The WP Extended flaw illustrates a recurring WordPress plugin pattern. Developers use string-matching functions (strpos, preg_match against URI) as access control. These functions check if a substring exists anywhere in the URI but do not validate the actual request target. A query parameter satisfies the check without affecting routing.
— Artem Safonov, Threat Analyst at AnonHaven
Quentn WP has SQL injection through a cookie. CVE-2026-2468 (CVSS 7.5) requires no authentication. The qntn_wp_access cookie is the injection vector. Cookie-based injection bypasses WAFs that only inspect GET/POST parameters. Most cloud WAF solutions skip cookies in default rules.
Font Manager / Custom Fonts has time-based blind SQL injection (CVE-2026-1800, CVSS 7.5). CMS Commander has multi-parameter injection via or_blogname and or_blogdescription (CVE-2026-3334, CVSS 8.8). myLinksDump has injection through sort parameters (CVE-2026-2279, CVSS 7.2, admin-level). Four injection vectors across four plugins in one weekend.
Five WordPress plugins contain privilege escalation at CVSS 8.1-8.8.
WP Extended (CVE-2026-4314), Linksy Search and Replace (CVE-2026-2941), and Expire Users (CVE-2026-4261) carry CVSS 8.8. Import and Export Users/Customers (CVE-2026-3629, CVSS 8.1) and App Builder / The Flight (CVE-2026-2375, CVSS 6.5) round out the cluster. All require only subscriber-level authentication.
The March 19 batch added two more at critical severity. WooCommerce Wholesale Lead Capture (CVE-2026-27542, CVSS 9.8) and BuilderPress (CVE-2026-27065, CVSS 9.8), both unauthenticated. Seven privilege escalation CVEs hit WordPress plugins in four days. Most plugins implement their own authorization logic rather than relying on WordPress core's capability system.
Seven privilege escalation CVEs in four days is not an anomaly. It is the steady-state output of an ecosystem where 60,000+ plugins each roll their own access control. The WordPress core capability API exists. Most plugin developers do not use it consistently.
— Artem Safonov, Threat Analyst at AnonHaven
SSRF flaws hit three plugins. MimeTypes Link Icons (CVE-2026-1313, CVSS 8.3), Content Syndicate Toolkit (CVE-2026-3478, CVSS 7.2), and Performance Monitor (CVE-2026-1648, CVSS 7.2) with Redis interaction. On cloud-hosted WordPress, Redis SSRF can reach internal metadata endpoints. JetFormBuilder has arbitrary file read via path traversal (CVE-2026-4373, CVSS 7.5). Invelity Product Feeds allows arbitrary file deletion (CVE-2025-14037, CVSS 8.1).
D-Link DHP-1320 firmware 1.00WWB04 has a buffer overflow (CVE-2026-4529, CVSS 7.4). The PowerLine router is end-of-life. D-Link will not patch it.
CISA and multiple national CERTs have recommended replacing discontinued D-Link hardware since early 2025. These devices remain in service because they still function and owners rarely track security advisories.
Four SQL injection bugs from 2019 received CVE identifiers this weekend. Kepler Wallpaper Script 1.1 (CVE-2019-25576, CVSS 8.8), ownDMS 4.7 (CVE-2019-25580, CVSS 8.8), phpTransformer 2016.9 (CVE-2019-25578, CVSS 8.8), and Green CMS 2.x (CVE-2019-25573, CVSS 7.1). No patches exist. The formal CVE assignment lets scanners flag these seven-year-old products. Decommission any instance found in production.
| Product | Action | Status |
|---|---|---|
| BACnet (CVE-2026-24060) | Segment BACnet traffic, encrypt at transport layer | Protocol-level, no patch |
| Memu Play 6.0.7 (CVE-2019-25568) | Update or restrict file permissions on install dir | Legacy, PoC public since 2019 |
| WP Extended (CVE-2026-4314) | Update via WordPress plugin trac | Patched |
| Quentn WP (CVE-2026-2468) | Add cookie to WAF inspection rules | Patch status unknown |
| CMS Commander (CVE-2026-3334) | Monitor for update | Patch status unknown |
| D-Link DHP-1320 (CVE-2026-4529) | Replace hardware | EOL, no patch |
| Legacy apps (2019 CVEs) | Decommission | No patch, unmaintained |
Audit installed WordPress plugins against this week's disclosure list. Enforce least privilege for user accounts. Subscriber accounts should not exist unless necessary, since five of the weekend's privilege escalation flaws require only that role. Monitor for unauthorized admin account creation. Add the qntn_wp_access cookie to WAF inspection rules if Quentn WP is installed. Decommission Kepler Wallpaper Script, ownDMS, phpTransformer, and Green CMS instances immediately.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







