The DOJ seized four domains run by Iran's MOIS on March 19, 2026. The move came eight days after Handala Hack claimed a wiper attack against Stryker Corporation, a $22 billion Michigan medtech company with 56,000 employees. Within hours, Handala launched a replacement domain on a Palestinian TLD.
Four domains served what the DOJ called "faketivist" psychological operations. Justicehomeland[.]org and Karmabelow80[.]org belonged to separate MOIS personas. Handala-hack[.]to and handala-redwanted[.]to belonged to Handala. The FBI linked all four through shared leak sites, Iranian IP ranges, and a common playbook combining destructive cyberattacks with selective leaks. The court-authorized warrant was issued by the US District Court for the District of Maryland. It drew in part on an FBI undercover investigation tracing back to the 2022 Albania cyberattack.
The Stryker attack is the centerpiece of the DOJ action. On March 11, 2026, at approximately 5:00 AM UTC, attackers executed a mass device-wipe command through Stryker's Microsoft Intune mobile device management (MDM) platform. They had hijacked an administrator account and created a new Global Administrator inside the company's Microsoft environment. Between 5:00 and 8:00 AM UTC, roughly 80,000 managed devices were erased.
No malware was involved. Stryker's SEC 8-K filing described "severe global disruption" but found "no indication of ransomware or malware." The attackers used legitimate enterprise tools to wipe servers, laptops, and mobile phones across multiple countries. Employees arrived at work to find devices blank. Some had personal phones enrolled through Stryker's BYOD program, which were also factory-reset, destroying photos, eSIMs, and authenticator apps. Investigators found no evidence of exfiltration.
Handala claimed it wiped over 200,000 devices across 79 countries and stole 50 terabytes of corporate data.
The FBI affidavit disclosed that the attack disrupted hospital systems in Maryland. Healthcare providers suspended connections to Stryker tools used to analyze patient records and vital signs. At least one employee's computer was wiped during active clinical use. Stryker said on March 19 that it had made "significant progress" restoring ordering and shipping capabilities, but some personalized-implant customers were still experiencing delays.
In its press release, the DOJ referred only to "a U.S.-based multinational medical technologies firm." A spokesperson later confirmed to Reuters that the FBI filing identified Handala as responsible for the Stryker attack.
We're grateful to the government for their efforts to seize domains linked to the purported threat actors.
— Stryker Corporation, March 19, 2026.
Handala's campaigns extended beyond destruction. US airstrikes against Iranian targets began February 28, 2026 (Operation Epic Fury), and Handala immediately escalated to targeting American entities. On March 1, the email account Handala_Team@outlook[.]com sent death threats to two Iranian dissidents living in the United States and abroad. The message declared allegiance to Supreme Leader Ali Hosseini Khamenei, disclosed the victims' home addresses, and offered a $250,000 bounty for their execution. It claimed that Mexico's Jalisco New Generation Cartel (CJNG) had been given a list of targets.
The CJNG reference carries weight beyond propaganda. On March 6, 2026, a US court convicted MOIS asset Asif Merchant of terrorism and murder for hire in a separate plot targeting American politicians. Iranian intelligence contracting cartel hitmen on US soil is not hypothetical but a documented prosecution.
Handala posted names and records of alleged IDF members through handala-hack[.]to on March 6. The same day, Handala claimed 851 gigabytes stolen from the Sanzer Hasidic Jewish community, accompanied by threats. By March 9, handala-redwanted[.]to hosted personal records of roughly 190 IDF and Israeli officials. Warnings stated that their home addresses were known and "consequences would soon follow."
Two remaining domains trace back four years. In July and September 2022, MOIS operatives used Justicehomeland[.]org to claim responsibility for destructive cyberattacks against Albanian government systems. The campaign targeted Albania for hosting members of the Mujahedeen-e-Khalq (MEK), an Iranian dissident group. Albania severed diplomatic relations with Iran that September, the first time a NATO member expelled Iranian diplomats over a cyberattack. Microsoft published a detailed MOIS attribution the same month.
The FBI's seizure affidavit ties all three brands to one operation. Handala, Homeland Justice, and Karma Below "are part of the same conspiracy because they are operated by the same individuals." Three brand identities, one state intelligence service.
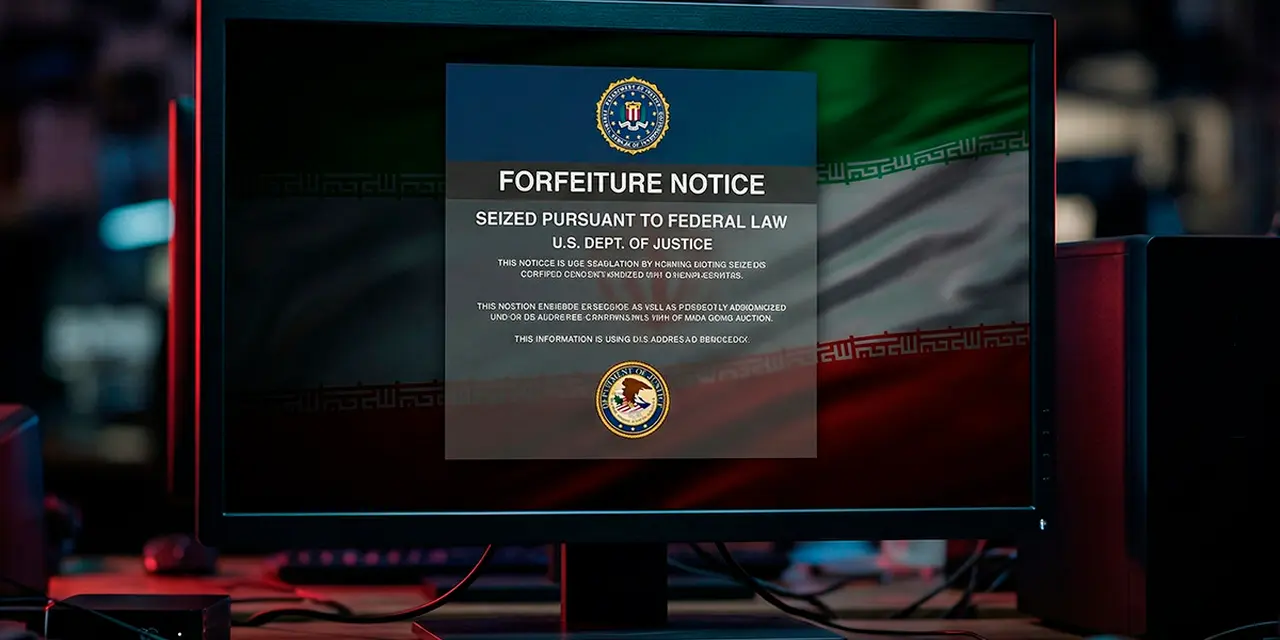
![FBI domain seizure banner on Handala Hack website showing Department of Justice and FBI logos FBI seizure banner displayed on handala-hack[.]to after the March 19 takedown.](https://anonhaven.com/media/uploads/2026/03/4d147262-5081-4376-ad6e-684b07134fb0.webp)
Handala Hack first appeared in December 2023. The name comes from a barefoot boy drawn by Palestinian cartoonist Naji al-Ali in 1969, a symbol of resistance. Despite presenting itself as a hacktivist front, the persona has been attributed to MOIS by multiple agencies. Check Point Research tracks the actor as Void Manticore. Microsoft classifies it as Storm-0842. CrowdStrike uses Banished Kitten.
Iranian researcher Nariman Gharib traced Handala to a cyber unit inside the MOIS counter-terrorism division. Its leader, Seyed Yahya Hosseini Panjaki (deputy minister), was sanctioned by the US Treasury in September 2024. The EU and UK followed with their own sanctions. Panjaki was added to the FBI terrorism watch list. Check Point reported he was "reportedly killed in the opening phase of Israel's strikes on Iran in early March 2026." Independent confirmation has not been published.
Reichman University researchers documented at least 85 claimed Handala attacks between February 2024 and February 2025. Targets spanned Israeli technology, defense, healthcare, and education sectors. In September 2024, Handala claimed a 197-gigabyte breach of the Soreq Nuclear Research Center. Israel's National Cyber Directorate assessed the claim as psychological warfare. A February 2025 claim of 2.1 terabytes from the Israeli Police was assessed as partially outdated material.
In January 2026, Handala infiltrated Maagar-Tec emergency alert systems at over 20 Israeli kindergartens. Air raid sirens activated. Threatening messages broadcast in Arabic.
Check Point's March 2026 report documented Handala's tradecraft in detail. The actors rely on manual, hands-on techniques using off-the-shelf wipers and publicly available deletion tools. Initial access comes through phishing campaigns impersonating trusted vendors (F5, CrowdStrike), compromised VPN accounts, and brute-force attacks against organizational VPN infrastructure. One newly observed technique used an AI-assisted PowerShell script for wiping activity. Handala maintained operational security through commercial VPN segments but exposed Iranian IP addresses when VPN connections dropped. Since Iran's January 2026 internet shutdown, Check Point observed the group routing through Starlink IP ranges to blend into satellite traffic.
The seizure's practical effect lasted hours. Handala posted a defiant statement on its 41st Telegram channel (after 40 prior suspensions). It called the action "desperate attempts by the United States and its allies to silence the voice of Handala." Its operators registered handala-hack[.]ps on a Palestinian country-code TLD. That replacement was also redirected to the FBI seizure notice shortly after.
Iranian threat actors, MOIS in particular, are no strangers to takedowns. Handala alone has had tens of Telegram channels, X accounts and domains taken down, and these takedowns have never slowed them down significantly.
— Ari Ben Am, adjunct fellow, Foundation for Defense of Democracies
Their organizational and management structure is currently disrupted, and at any moment, members of this group may be targeted by missile strikes, just like other cyber forces of the regime.
— Nariman Gharib, Iranian activist and independent cyber-espionage investigator.
Washington's Rewards for Justice program offered up to $10 million for information on MOIS-linked operators.
The filing formally attributed Handala to MOIS for the first time during the current US-Iran conflict. The court filings tying three personas to the same operators and the same Iranian IP ranges carry more value than the seized domains. For network defenders, the indicators of compromise in the unsealed filings matter most.
Organizations running Microsoft Intune or any cloud-based MDM should audit Global Administrator accounts immediately. Enforce phishing-resistant MFA (FIDO2 or certificate-based). Enable multi-person approval for destructive commands like remote wipe. Intune supports this natively. A single stolen admin credential erased 80,000 Stryker endpoints in three hours without deploying any malware.
Have a story? Become a contributor.
We work with independent researchers and cybersecurity professionals. Send us a tip or submit your article for editorial review.







